Google Directory Service integration is currently not supported for Barracuda Cloud Archiving Service.
You must configure LDAP or Microsoft Entra ID for group expansion and user attributes in the Barracuda Cloud Archiving Service.
Active Directory Limitations
Barracuda Networks does not support using default AD groups, such as Domain Users, when applying entitlements for user access. Due to limitations within AD, these groups may not contain all users or any users at all.
Verify User Status
Before adding users to the Barracuda Cloud Archiving Service via your organization's LDAP servers, verify that users are enabled, are members of the domain, and that the mail attribute is set for each user.
Incoming Connections
To ensure uninterrupted access to LDAP server from the Barracuda Cloud, you must allow incoming connections from the following IP ranges:
- 209.222.80.0/21
- 64.235.144.0/20
- 35.170.131.81
- 54.156.244.63
- 54.209.169.44
Secure LDAP
Barracuda Networks recommends connecting your LDAP connection using SSL (LDAPS). As the information will be transmitted between Barracuda Networks' cloud servers and your Cloud email service, you must ensure that the connection is secure. Contact your IT Administrator if you need help setting up LDAPS in your network.
Use AD authentication to store and administer Barracuda Cloud Archiving Service user accounts via your organization's LDAP or Microsoft Entra ID.
When you first set up the Barracuda Cloud Archiving Service, a warning notice displays across the top of the web interface notifying you that you must configure AD through Barracuda Cloud Control and enable groups. Before you continue, you are required to either set up AD and wait for a sync to complete, or select to proceed without AD. Barracuda Networks strongly recommends setting up local AD.
Create a Barracuda Cloud Control Directory
- Log into https://login.barracudanetworks.com/ as the account administrator, and go to Home > Admin > Directories.
- Click the Add Directory button.

- Select one of the following sections to add a new LDAP or Microsoft Entra ID.
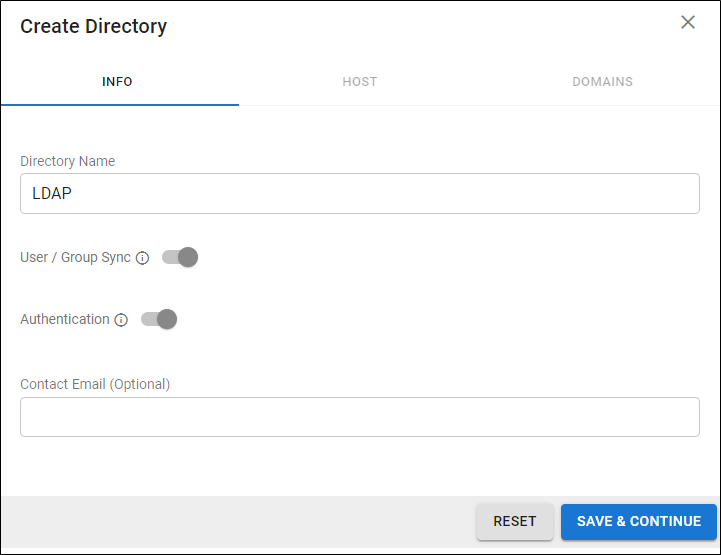
Add a New LDAP Active Directory
- Select LDAP Active Directory.
- On the INFO tab, specify a new Directory Name.
-
Activate the Authentication option to have users authenticate using their LDAP credentials. If you disable this option, users authenticate with Barracuda Cloud Control.
Barracuda Networks strongly recommends creating an additional administrator account using an independent domain that does not use Active Directory (AD) authentication. This allows you access to your Barracuda Networks product account if your AD server goes down or fails.
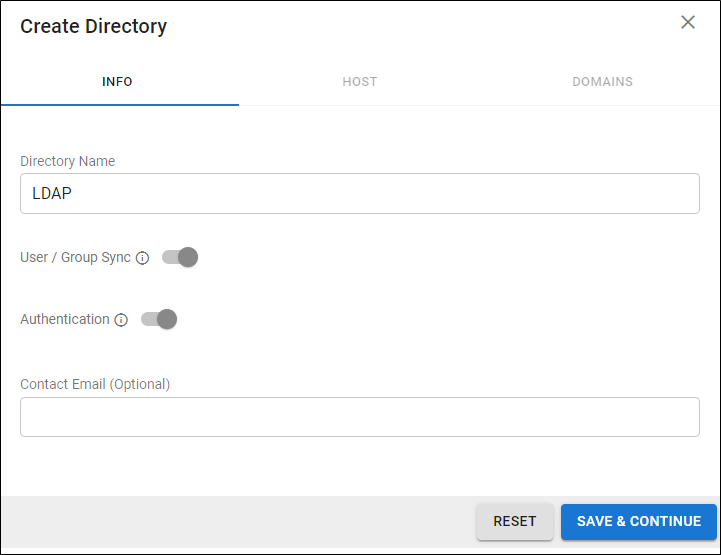
- Click SAVE AND CONTINUE.
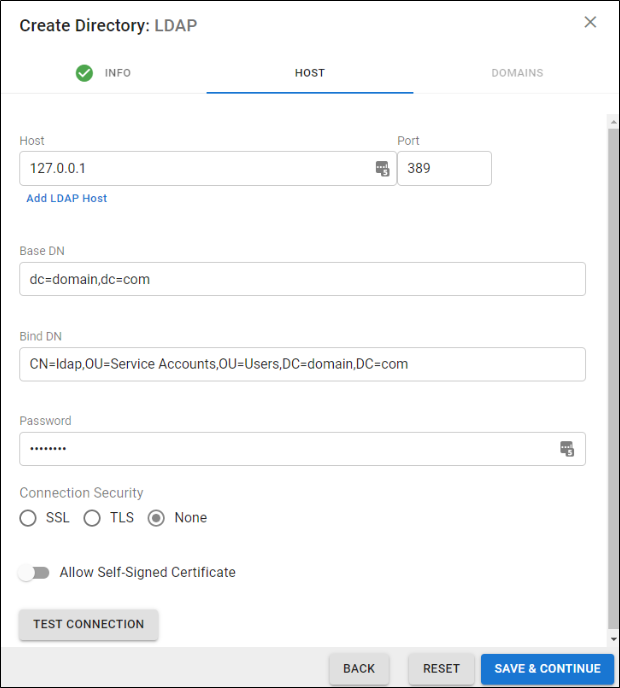
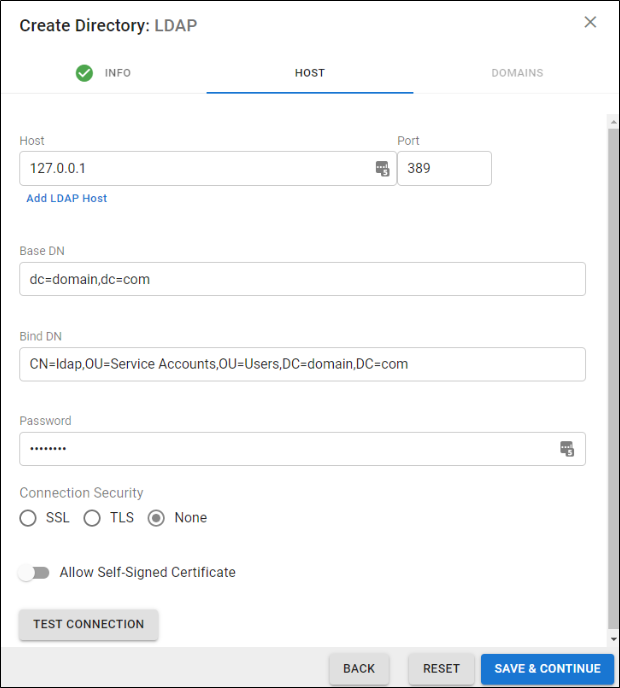
- On the HOST tab, specify the following for the LDAP host:
-
LDAP Host IP address
-
LDAP Host Port – Use Port 389 for LDAP and LDAPTLS or Port 636 for LDAPS.
-
Base Domain Name (DN) – Any user or group that exists with the search base that will sync to Barracuda Networks. For example,
DC=domain,DC=com.
-
Bind DN – Enter the bind domain name for a service account with read permissions to the active directory.
-
Password – Password associated with the service account.
-
Connection Security – Select SSL, TLS, or None. For more information, see New Requirements for LDAP Authentication.
-
(Optional) To add additional servers, click Add LDAP Host.
- If your LDAP server uses a self-signed certificate, toggle on the Allow Self-Signed Certificate setting.
- Click TEST CONNECTION to check connectivity to the host. If the connection fails, verify your settings are correct and that you have allowed the Barracuda Networks IP in your firewall. Contact Barracuda Networks Technical Support for additional troubleshooting.
- If the connection succeeds, it displays as Connected. Click SAVE AND CONTINUE.
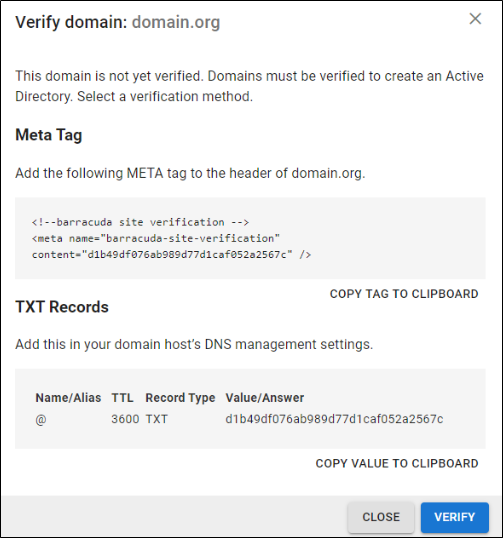
- On the DOMAINS tab, add the domains associated with your users.
- For each domain that you add, click Verify and following the instructions to verify the domain.
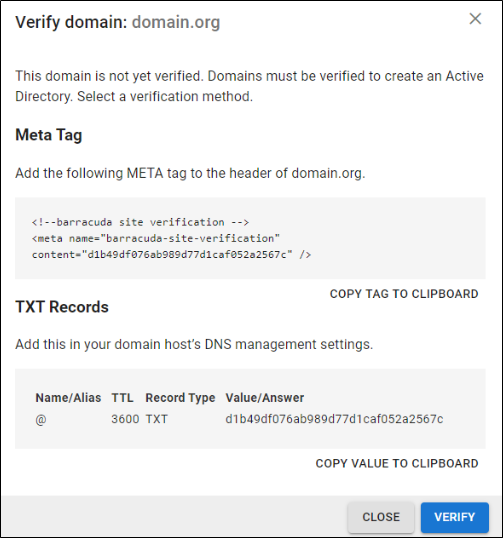
- After each domain is verified, you can sync your users and groups to the Barracuda Cloud Control.
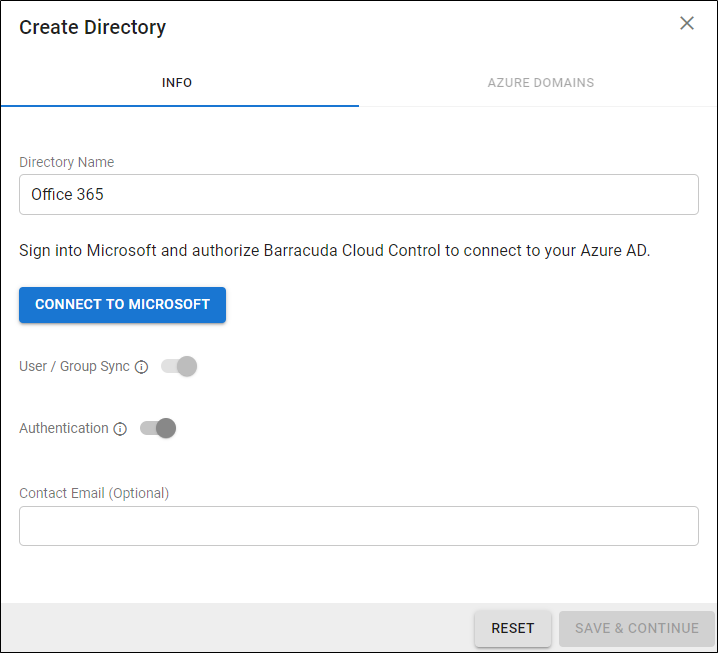
Add a New Microsoft Entra ID
- Select Azure Active Directory (now Microsoft Entra ID).
- On the INFO tab, specify a new Directory Name. For example, "Office 365".
- Click CONNECT TO MICROSOFT to sign into Microsoft and authorize Barracuda Cloud Control to connect to your Microsoft Entra ID.
- Log in with your Microsoft 365 administrator credentials.
- Accept the credentials for the application request.
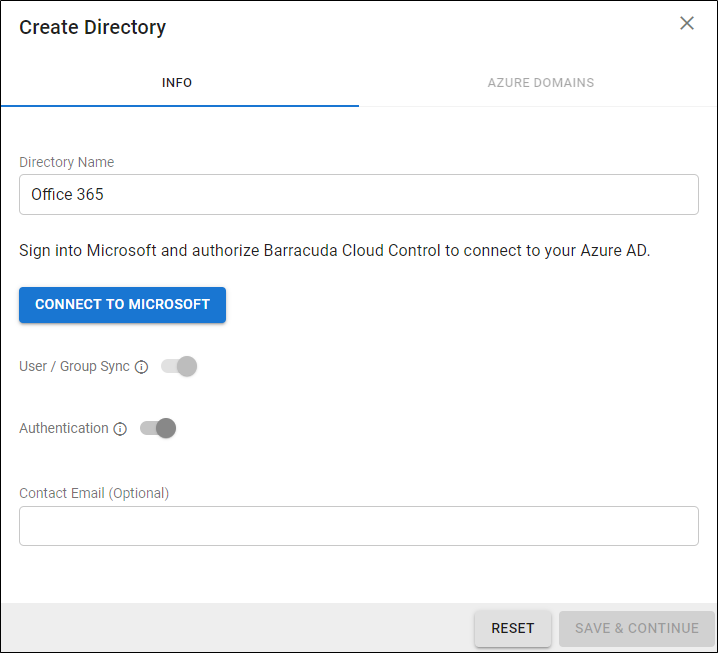
-
Activate the Authentication option to have users authenticate using their Azure credentials. If you disable this option, users authenticate with Barracuda Cloud Control.
Barracuda Networks strongly recommends creating an additional administrator account using an independent domain that does not use Active Directory (AD) authentication. This allows you access to your Barracuda Networks product account if your AD server goes down or fails.
- After you are redirected back to the Barracuda Cloud Control, click Save.
For end-user authentication, refer to How to Set Up Active Directory Groups for End-User Authentication.