This section walks you through steps of how to deploy Barracuda WAF on OpenStack.
Getting Started
OpenStack is an open source cloud computing platform for public and private clouds. They provide infrastructure as a service on which administrators can run virtual servers,services and other resources.
Barracuda Web Application Firewall is deployed on OpenStack as a virtual machine and protects web applications running on OpenStack as well as external web applications.
Deploying and Provisioning the Barracuda Web Application Firewall on OpenStack
The following instructions have been written with respect to OpenStack Horizon dashboard.
Before you begin to verify if the following pre-requisites are met:
Create an account with access to -OpenStack nova for computing, neutron for networking, glance for uploading an image.
Upload the Barracuda WAF Vx image for KVM/QEMU to Openstack.
A functional openstack platform with
- At least one network with access to the internet
- Availability zone
- Instance flavors
A valid key pair on Openstack
A security group allowing inbound access to the following network ports:
Inbound:
TCP 8000
TCP 80
TCP 8443
TCP 443
Outbound:
TCP 8000
TCP 443
TCP 80
ICMP
Basic Provisioning
Using the GUI
Log into OpenStack dashboard.
Click Instances from the left pane.
Click Launch Instance. The Launch Instance page appears. Provide the following details in the respective sections.
Details:
Instance Name - hostname for the instance
Description - Description of the instance
Availability Zone - availability zone where the instance is deployed
Count – the number of instances that need to be created
Source:
Select Boot Source – option selected to boot the instance. Here, the option “Image” is used to boot the instance. Click the arrow provided next to the instance to allocate for booting.
Flavor:
Flavors selected for an instance determines the amount of computing, storage and memory resources that will be carved out for the instance. Click the arrow provided next to the flavor to allocate enough resources to support the type of instance you are trying to create.
Networks:
Networks selected to provide the communication channels for instances in the cloud. Click the arrow provided next to the network to use this network for communication.
Network Ports:
Ports selected for providing extra communication channels to your instances. Instances attach their interfaces to ports. You can select ports instead of networks or a mix of both. Click the arrow provided next to the port to attach the IP address(es) to the interfaces plugged into them.
Security Groups:
The security group selected to launch the instance.
Key Pair:
Key pairs selected to allow you to SSH into your newly created instance. You can select an existing key pair, import a key pair, or generate a new key pair.
Using the CLI
To deploy a Barracuda Web Application Firewall, you must launch an instance. This instance serves as a virtual machine.
| Arguments | Values |
|---|---|
| flavor | <flavor type> |
| Image | <image name> |
| nic net-id | <port ID> |
| security-group | <security group name> |
| key-name | <key pair name> |
Set the environment variables using the Openstack RC file:
- On the API Access tab, click Download OpenStack RC File and save the file. The filename will be in the form "PROJECT-openrc.sh" where PROJECT is the name of the project for which you downloaded the file.To use the demo user profile: #. demo-openrc .
- Gathering the required information before launching the instance:
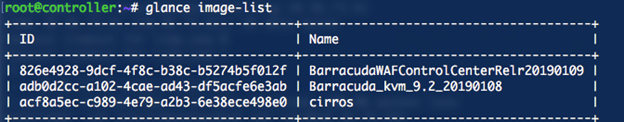
To launch an instance, you must choose a flavor and an image. The flavor represents the size of the instance, including the number of CPUs and amount of RAM and disk space. An image is a prepared OS installation from which you clone your instance.- To list the images: # glance image-list.
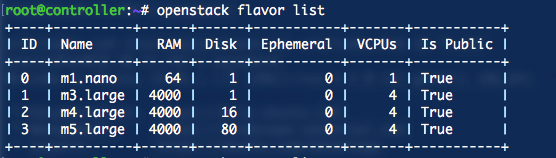
- To list the instance types: # openstackflavorlist.
- Check the available networks.
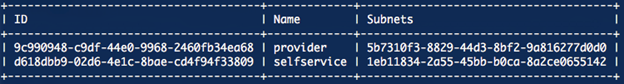
To list the networks: # openstack network list.
In the example below, two networks are created (selfservice and provider) and instances can be launched instances in either of them.
- To list the images: # glance image-list.
Command to create a VM
openstack server create --flavor m5.large --image Barracuda_kvm_9.2_20190108 --nic net-id=d618dbb9-02d6-4e1c-8bae-cd4f94f33809 --security-group default --key-name mykey barracudawafNew-instance. This will launch the VM in the self service network.
Advanced Provisioning
Barracuda WAF supports provisioning using metadata from a configuration drive. WAF mounts this drive during bootup and read files from it to get bootup information. This information is different from user data. Configuration drive can be used to pass networking, licensing as well as configuration import details to the WAF.
Booting up a WAF VM on Openstack and Assigning a Static IP
To provision the instance with a static IP, ensure the following pre-requisites are met:
- The port is configured on OpenStack
- A JSON file with the name “network.json” is created. This file contains the interface settings as per the port configuration mentioned above in point 1.
Sample JSON :
{
"address" : "192.168.200.25",
"netmask" : "255.255.255.0",
"gateway" : "192.168.200.200",
"dns" : "10.8.1.90"
}
Command to provision the instance:
Note: The following command must be run from the directory in which the network.json file is located:openstack server create --flavor m5.large --image Barracuda_kvm_9.2_20190108 --nic net-id=d618dbb9-02d6-4e1c-8bae-cd4f94f33809 --security-group default --key-name mykey –config-drive true --file network=network.json barracudawaf-static-ip
Result:
An instance is provisioned with the network details mentioned in the network.json file.
Bootstrapping a WAF VM with licensing, WCC details and configuration import on Openstack
To provision the instance with bootstrapping instructions, ensure the following pre-requisites are met:
- A fully functional WCCinstancewithatleastoneaccountadmin.
- The neutron port is configured on OpenStack.
To create the port with a fixed IP, use the following command: neutron port-create <network> --fixed-ip subnet_id=<subnet_id>,ip_address=<fixed-ip>
where,
subnet_id is the subnet that the port is part of and ip_address isthefixedipinthesubnet that should be allocated to the port. - A JSON file with the name “network.json” is created. Thisfilecontainstheinterfacesettingsasper the port configuration mentioned above in point 2.
- WAF configuration file is imported into the system .
- Bootstrapping details in a file barracudaConf.json.
Sample JSON
{
"licenseFile" :
{
"releaseLicenseOnShutDown"
: "no",
"accessType"
: "wcc",
"host"
: "192.168.200.9",
"hostPort"
: "443"
},
"eulaSignature" :
{
"name"
: "test",
"email"
: "test@abc.com",
"company"
: "Barracuda Networks"
},
"wccDetails" :
{
"wccIpAddress"
: "192.168.200.9",
"wccPassword"
: "admin123",
"wccUserName"
: "demo@cuda.local",
"wccValidationToken"
: "rmRcCnDU"
},
"guiAdminPassword" : "admin",
"systemTimezone" :
"America/Los_Angeles",
"defaultDomain" :
"cuda.local",
"bootstrap-method" : "config-json"
}The barracudaConf.json configuration parameters are listed in the table below:
| Configuration parameter | Description | |
|---|---|---|
| LicenseFile | ||
| releaseLicenseOnShutDown | Instructs the WAF to release the license during shutdown or termination.Values:
| |
| accessType | Sourcefrom wherelicenseis retrievedValue:
| |
| host | The ip address of the WCC unit | |
| hostPort | The port to be used to connect to the WCC instance | |
| eulaSignature | ||
| name | The contact name for end user license agreement | |
| Email address of the user | ||
| company | Company details of the user | |
| wccDetails | The details of the account to which the WAF should be associated | |
| wccIpAddress | IP Address of the WCC instance | |
| wccPassword | Password of the account | |
| wccUserName | Username of the account | |
| wccValidationToken | Token generated for the account | |
guiAdminPassword | WAF admin password | |
systemTimezone | Time zone for the WAF unit | |
defaultDomain | Domain name for the WAF | |
bootstrap-method | Bootstrapping method for the WAF:Values:
|
Command:
The following command should be run from the directory in which the files, barracudaConf.json, apiConfig.jsonandnetwork.json are located:
openstack server create --flavor m5.large --image Barracuda_kvm_9.2_20190108 --nic net-id=d618dbb9-02d6-4e1c-8bae-cd4f94f33809 --security-group default --key-name mykey –config-drive true --file network=network.json --file barracudaConf=barracudaConf.json --file configFile=apiConfig.json barracudawaf-static-ip.
Result:
An instance is provisioned with the network and bootstrapping details mentioned in the JSON file.
