Use the steps in this article to resolve the error "Unable to validate all permissions with AWS. For assistance with this issue, please contact Barracuda Networks Technical Support."
If you are replicating data offsite to AWS and are unable to validate AWS credentials, these steps will determine if an SCP policy is blocking the simulator.
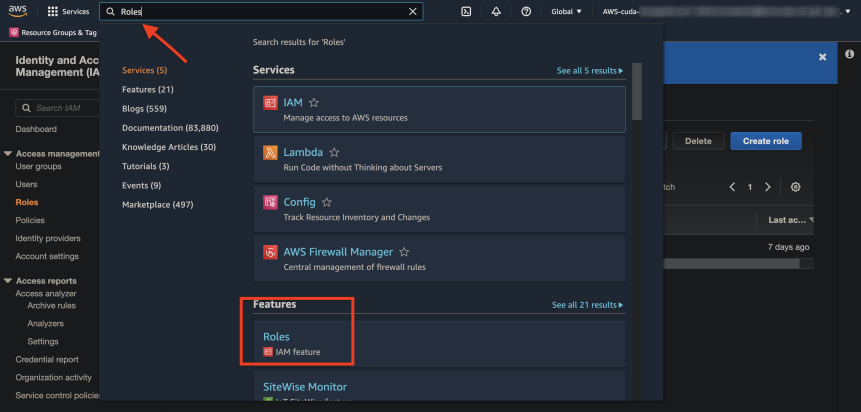
- Log into AWS and search for "Roles" in the search bar. Under Features, click Roles - IAM feature.
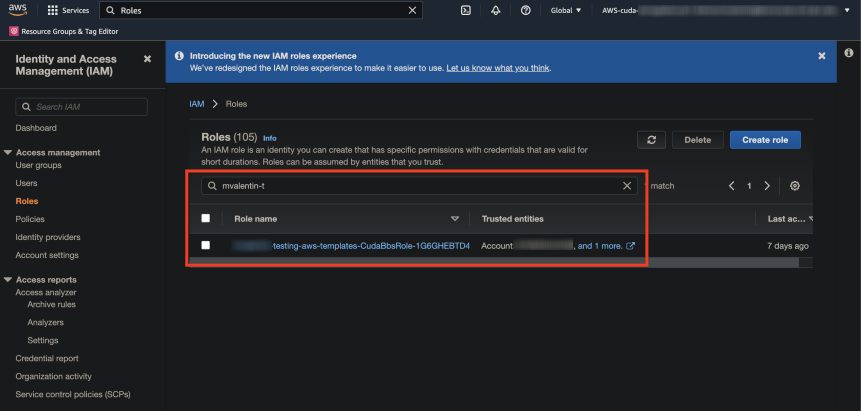
- Filter using the IAM Role you imported with the template, and then click the Role name link.
- Scroll down and verify the Permissions policies. You should see Provides full access for S3 and EC2. If these are correct, click Simulate.
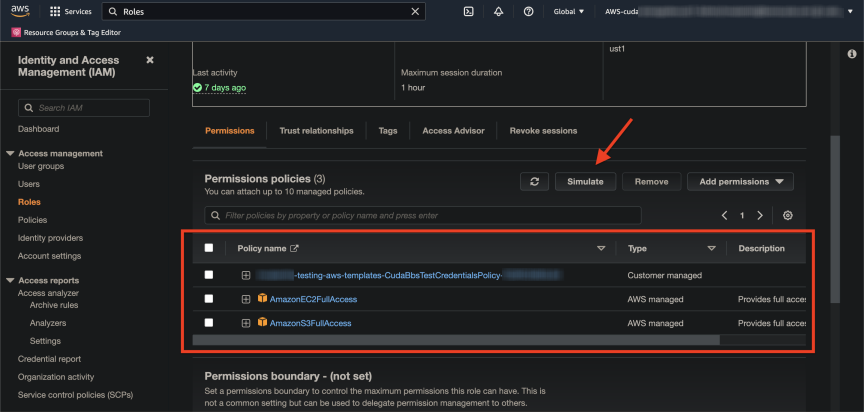
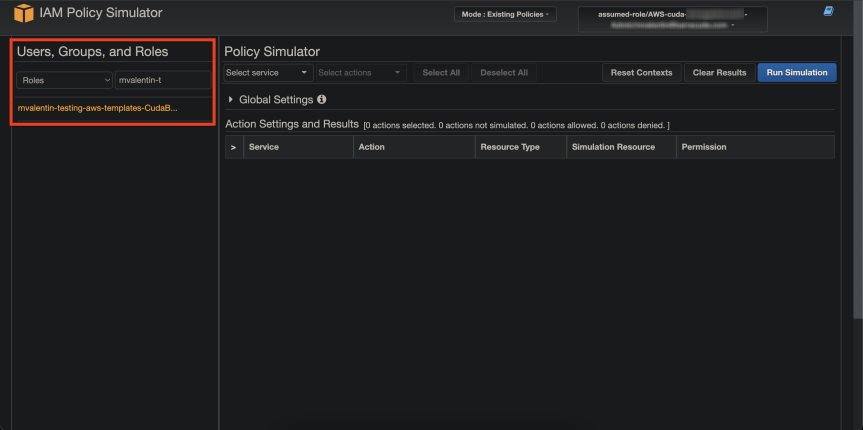
- On the top left of the IAM Policy Simulator page, change the first dropdown menu to Roles and enter the role you are searching for in the second filter box. Click on the role in the filtered results.
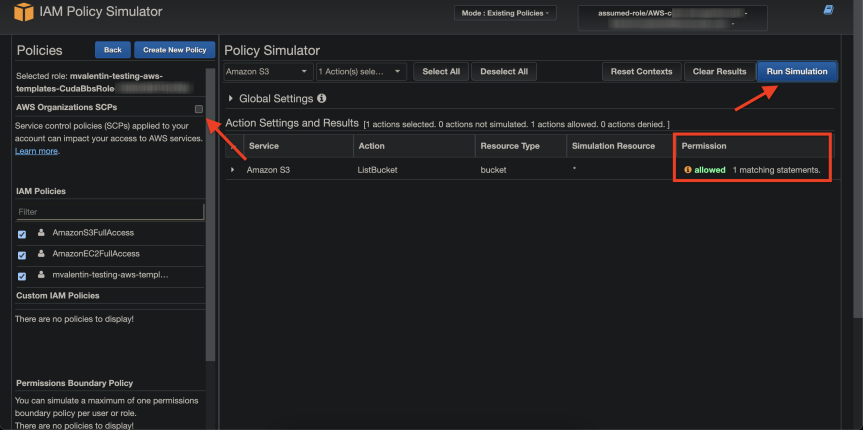
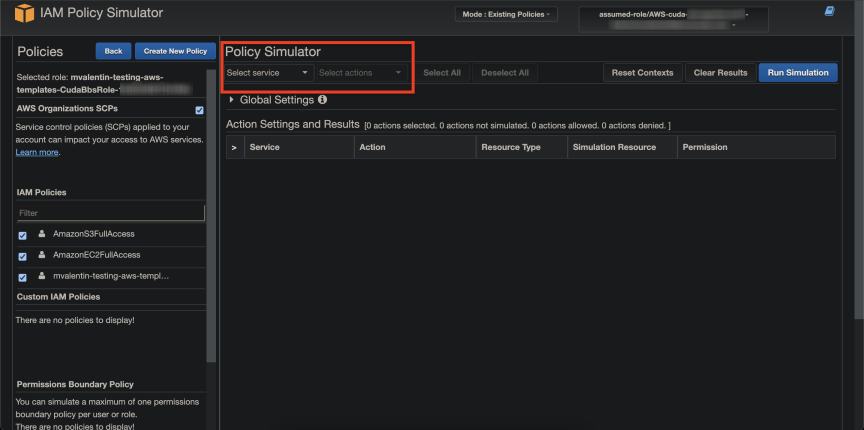
- Under the Policy Simulator section, change the first dropdown Select service menu to S3. Change the second dropdown Select actions menu to ListBucket.
- Click Run Simulation.
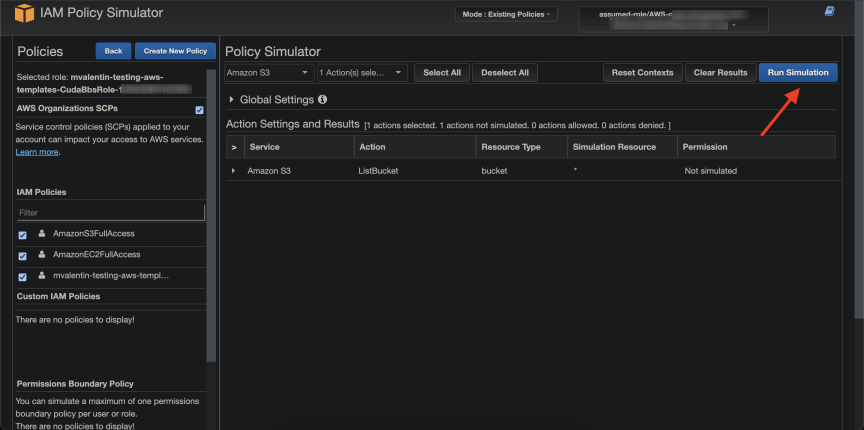
- If the result comes back Permission denied, it is possible that the permissions are incorrect or there is a global SCP policy restricting the region. The simulator does not know how to filter the region so it comes back with a denied error.
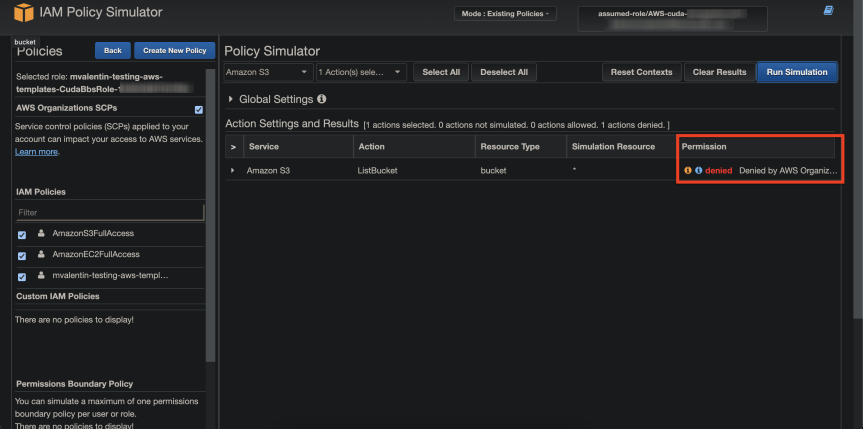
- If an organizational SCP is in place, the simulator will not be able to validate permissions. However, the real API calls will work. To verify, do the following:
- Uncheck the AWS Organization SCPs box under the Policies section on the left-hand side.
- Run the simulation again. You should now see Permission allowed. That means that the API calls will work properly when credentials are added. The API/SDK's available do not allow Barracuda Networks to uncheck this box like the web simulator, hence we are unable to validate permissions properly when SCPs restricting regions are in place. If the bug filed with AWS is fixed, we can validate permissions again with the simulator by ignoring SCPs. For more information, refer to https://github.com/aws/aws-sdk/issues/102.