The following article describes the working mechanism of Proxy and FTP gateway integration when using a virus scanner.
Proxy Integration
The Squid-based proxy service communicates with the virus scanner using ICAP protocol.
Schematic overview of proxy integration
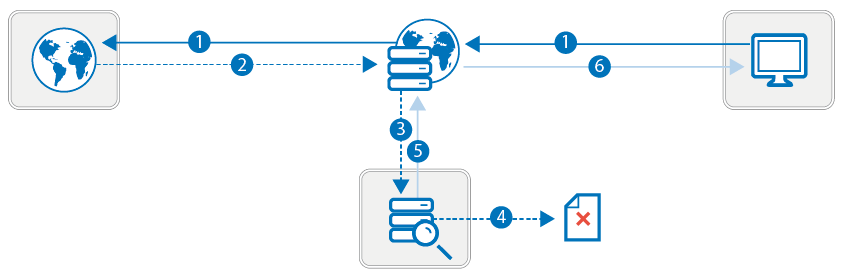
Proxy integration works as follows:
- The request is sent from the source address to the Internet.
- The response is returned from the destination.
- The response is forwarded to the antivirus service via ICAP.
- If content is "infected," it is removed.
- The scanned response is returned to the Barracuda CloudGen Firewall. In case of infected content, a corresponding block HTML page is sent.
- The requested content is delivered to source address. In case of infected content, a corresponding block HTML page is displayed.
To integrate virus scanning on an HTTP proxy, make sure that Yes is selected from the Enable Virus Scanning list in the HTTP Proxy Malware Protection settings.
FTP Gateway Integration
Scanning FTP requests is processed via internal service communication between the FTP gateway and the virus scanner service.
Schematic overview of FTP gateway integration
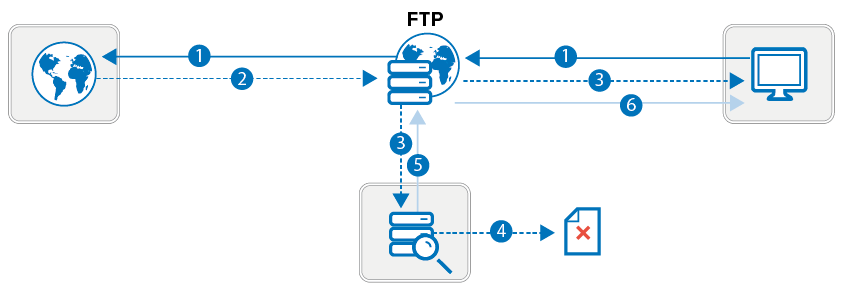
FTP Gateway integration works as follows
- The FTP request is sent from the client to the Internet, passing the FTP gateway.
- The response is returned from the destination to the FTP gateway.
- The response is split into two information streams. For every 4096 KB package, 1 KB is directly returned to the client without being scanned in order to avoid time-outs in the connection between the client and FTP gateway. The larger part of the data package is forwarded to the antivirus service.
- If content is "infected," it is removed. The virus scanner returns an error code and virus information to the FTP gateway, terminating the client data connection. Furthermore, it returns a 505 error code containing the virus information. The FTP gateway forwards this information to the client (505 virus <virus_name> found in file). The unscanned part of the data package, which has already been forwarded to the client, remains on it as tiny file fragment. This fragment must be deleted manually.
- If content is clean, the scanned response is returned to the FTP gateway.
- The FTP gateway delivers the requested content to the source client.
