The following example explains Azure active-active deployment with symmetric load balancing and User Defined Routing (UDR). With this setup, all traffic coming from the virtual networks hits the load balancer and will be distributed to the firewall units according to the rules configured in the template. Traffic from the firewalls, in turn, back to the networks does not require any translation and is processed by the firewall rules and therefore sent back to the correct recipient.
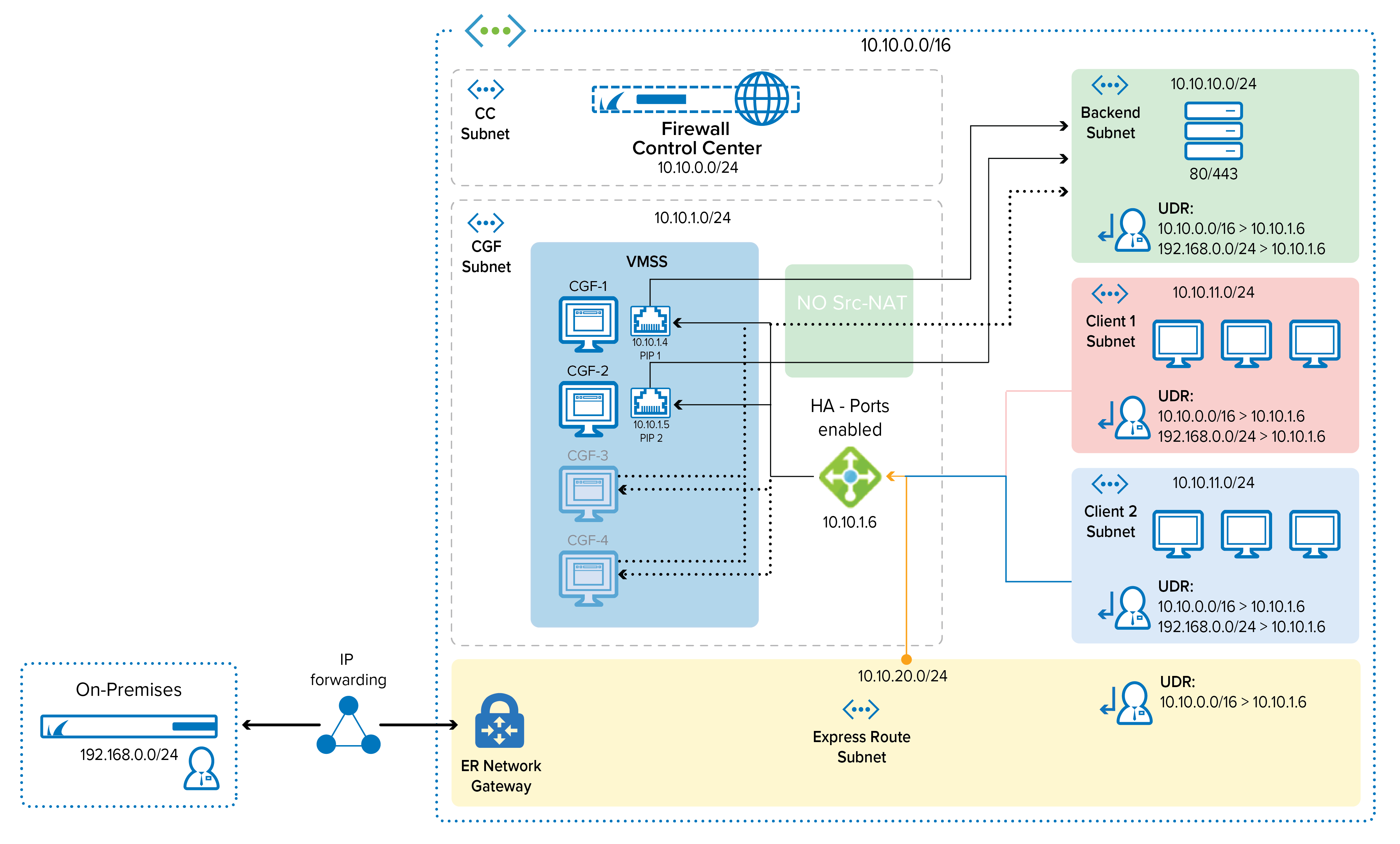
Azure active-active performance deployment with symmetric load balancing provides the following advantages:
Integrates well with network infrastructures using UDR and Azure Express Route
Does not require NAT
Extremely straightforward (add VMs to the backend pool, no other modifications required)
The CloudGen Firewall configuration in Microsoft Azure supports repositories, conf templates, and the distributed firewall. For more information, see Repositories, Distributed Firewall and How to Work with Configuration Templates on Different Levels in the Configuration Tree.
Before You Begin
Before proceeding with deploying the Barracuda CloudGen Firewall HA template, make sure that your network infrastructure meets the service requirements listed in CloudGen Firewall Active-Active Performance in Microsoft Azure.
The following preparatory steps will therefore serve as a guideline for understanding how to configure a setup regardless of the location of the related navigation items in the UI:
Creating resource groups
Creating a storage account
Creating a virtual network (VNET) and subnet(s)
Deploying a virtual CGF from an image
For more information, see How to Create a Resource Network in Azure.
Preparatory Steps
The following steps are illustrated only by their resulting screenshots from Azure management panel.
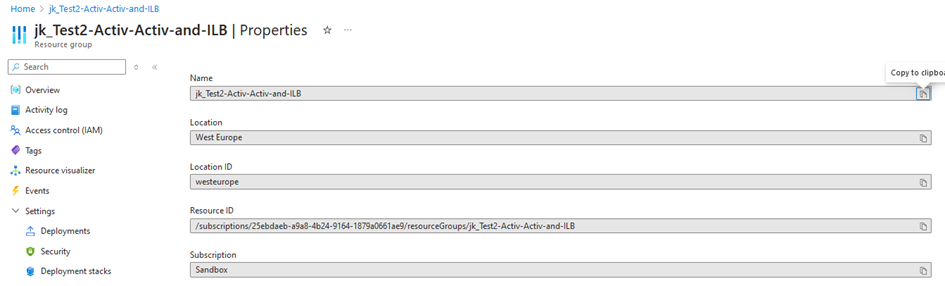
Create Resource Groups
Configure the following fields:
Name
Location
Location ID
Resource ID
Subscription
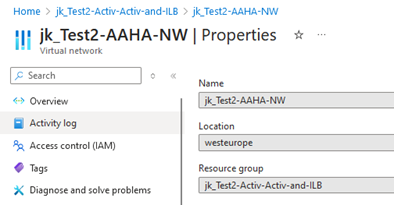
Create a Virtual Network
Configure the fields for the properties of your virtual network:
Name
Location
Resource Group
Configure the Address space of your virtual network:
Address space
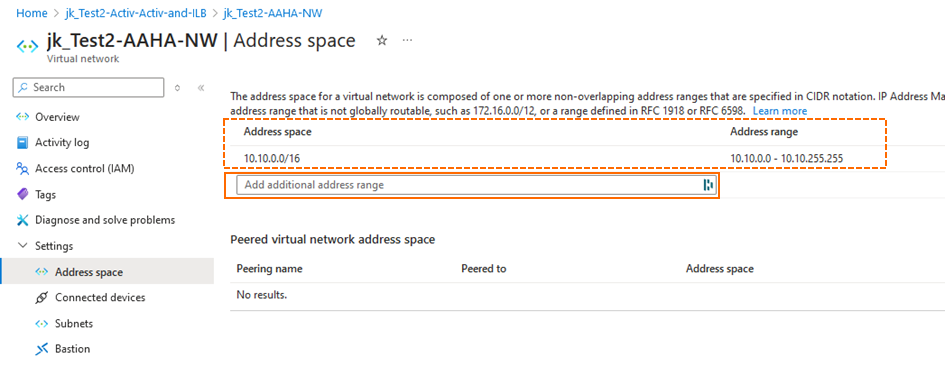
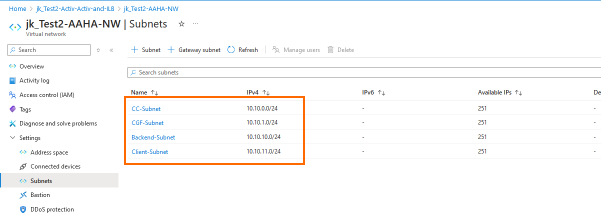
Configure the Subnets:
Subnets
After configuring the basic resources, it is now time for creating a Virtual Machine Scale Set. The configured basic resources from above will be used in the following configuration steps.
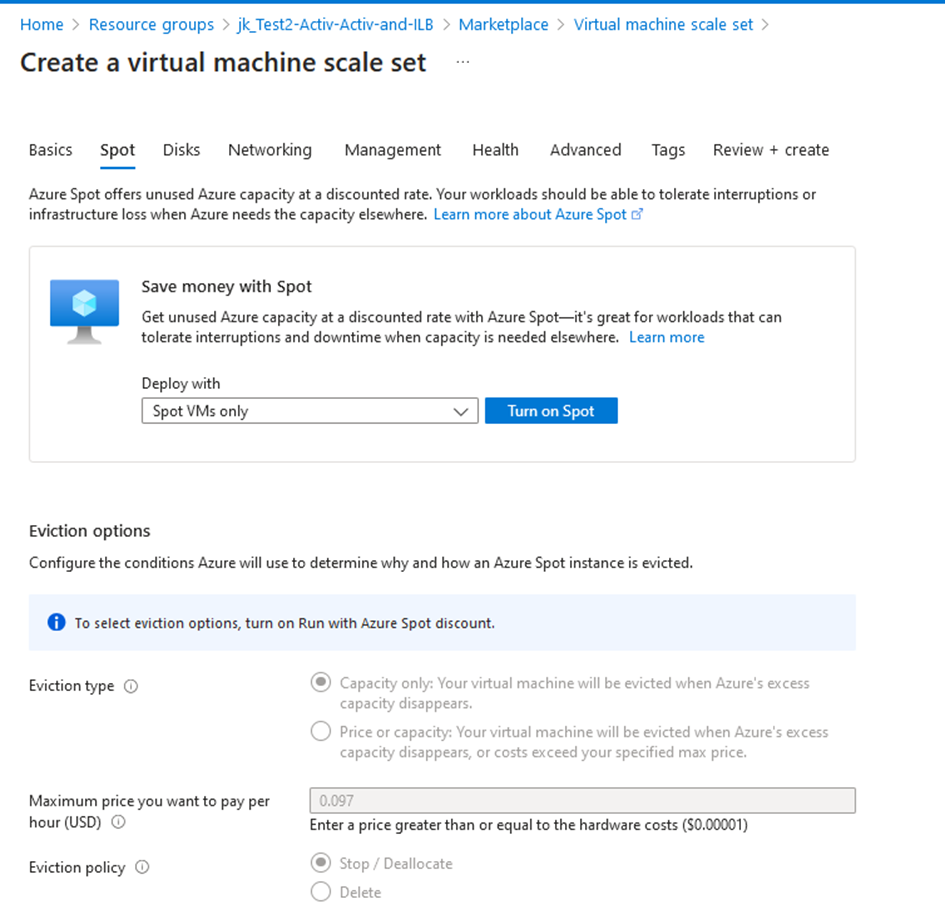
1. Create a Virtual Machine Scale Set
Step 1. Click Basic to Configure a Barracuda Virtual Machine Scale Set
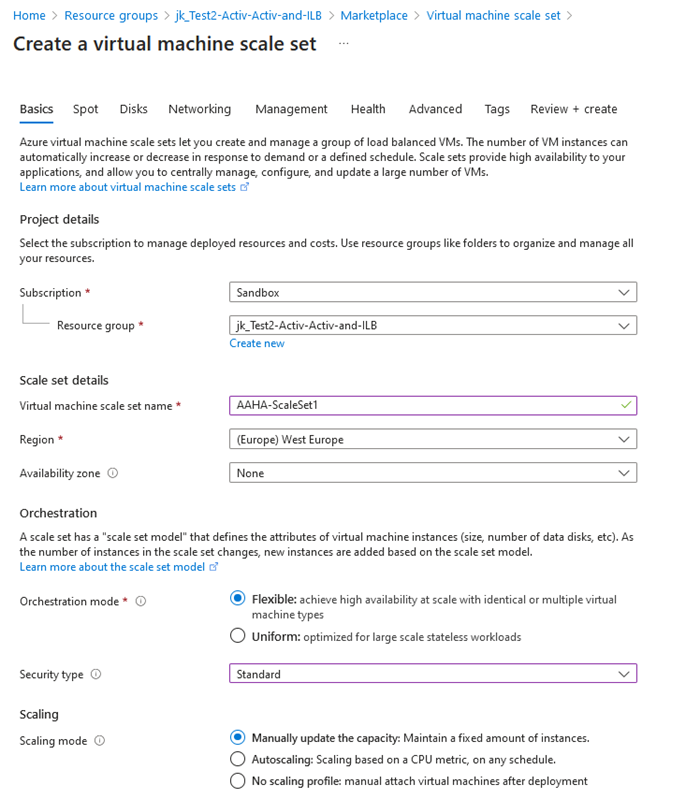
Step 2. Scroll Down and Configure Scaling
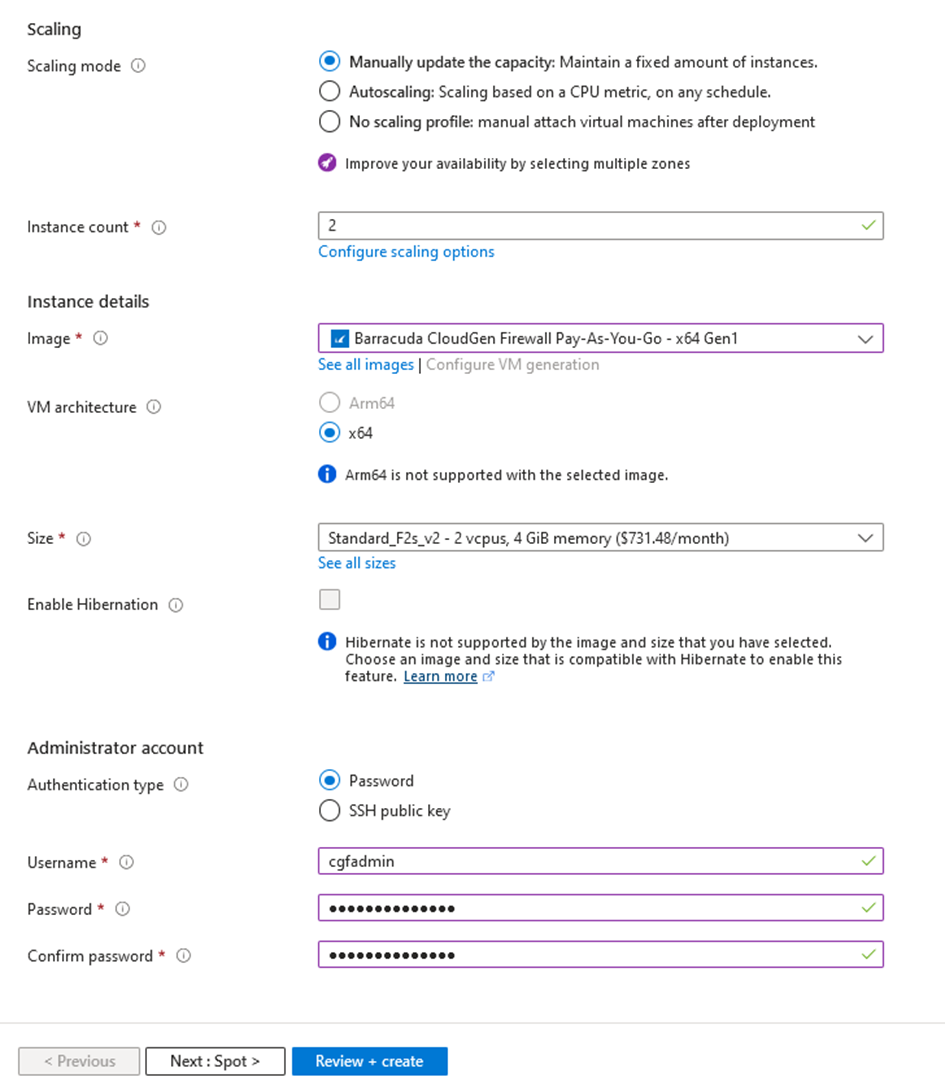
Step 3. (optional) Click Next:Spot> to Deploy the Virtual Machine as a Sport Instance
The Spot VM option allows customers to buy the VM from a pool of unused spare capacity at a lower price than a pay-as-you-go option. However, this lower price comes with the drawback that such spot instances can be taken away without any major warning if the capacity is needed elsewhere. Therefore, it is recommended to not use this option.
If you want to use this spot even though, configure it according to the screenshot below.
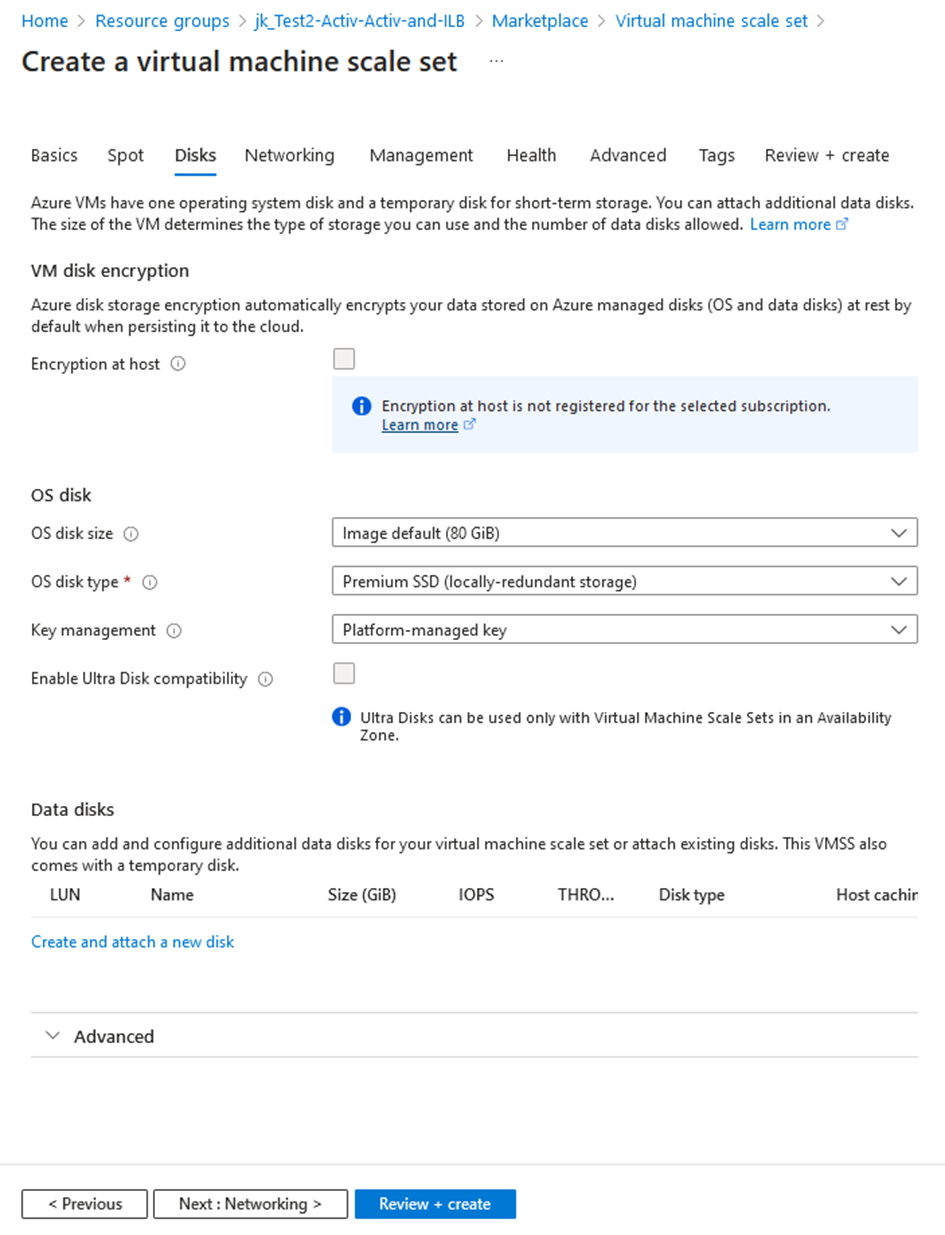
Step 4. Click and Set up Disks according to Your Requirements
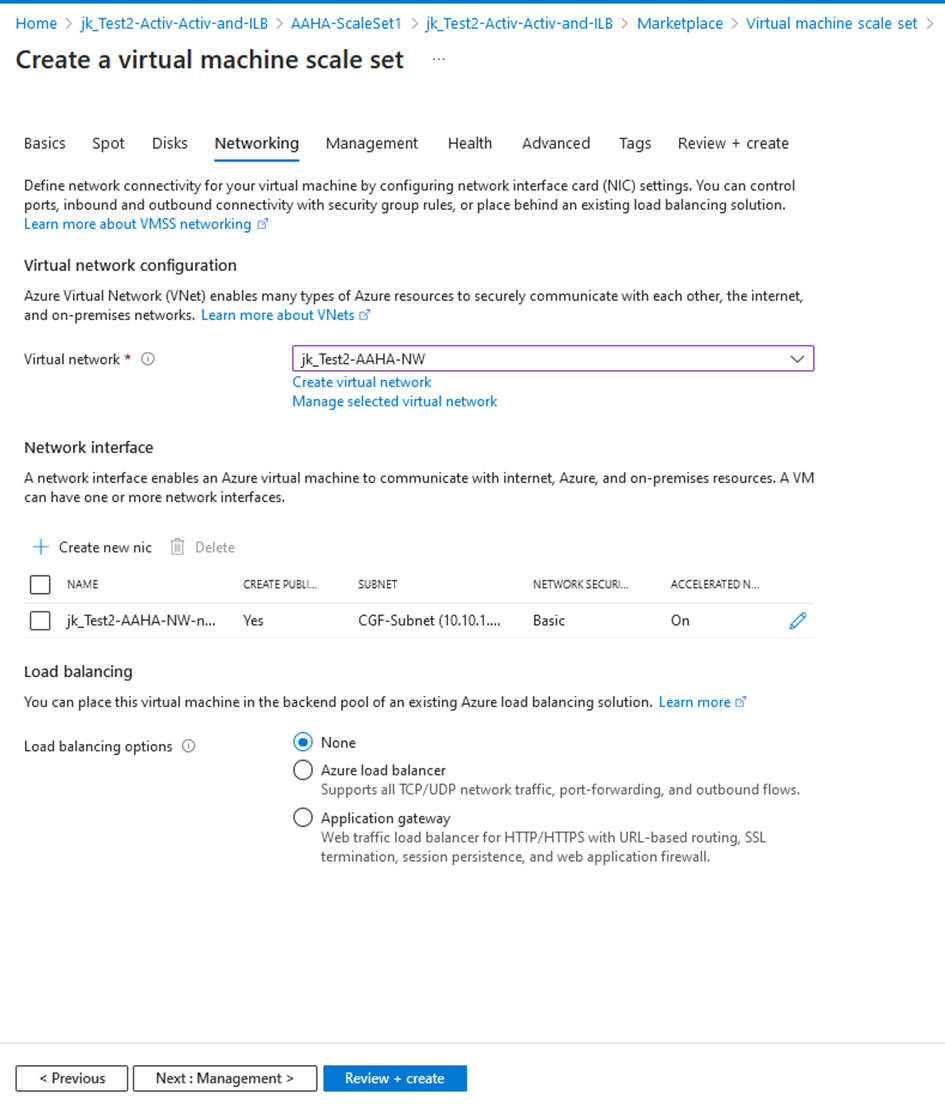
Step 5. Click and Configure Networking
Enter the name for your Virtual Network
Click '+' to configure the Network Interface
Enter the network address for your subnet.
Select Basic for your NIC network security group.
Enter the name for your subnet, e.g., CGF-Subnet (10.10.1.0/24)
Select None for Public Inbound Ports.
Select Enabled for Publish IP Address.
Select Enabled for Accelerated Networking.
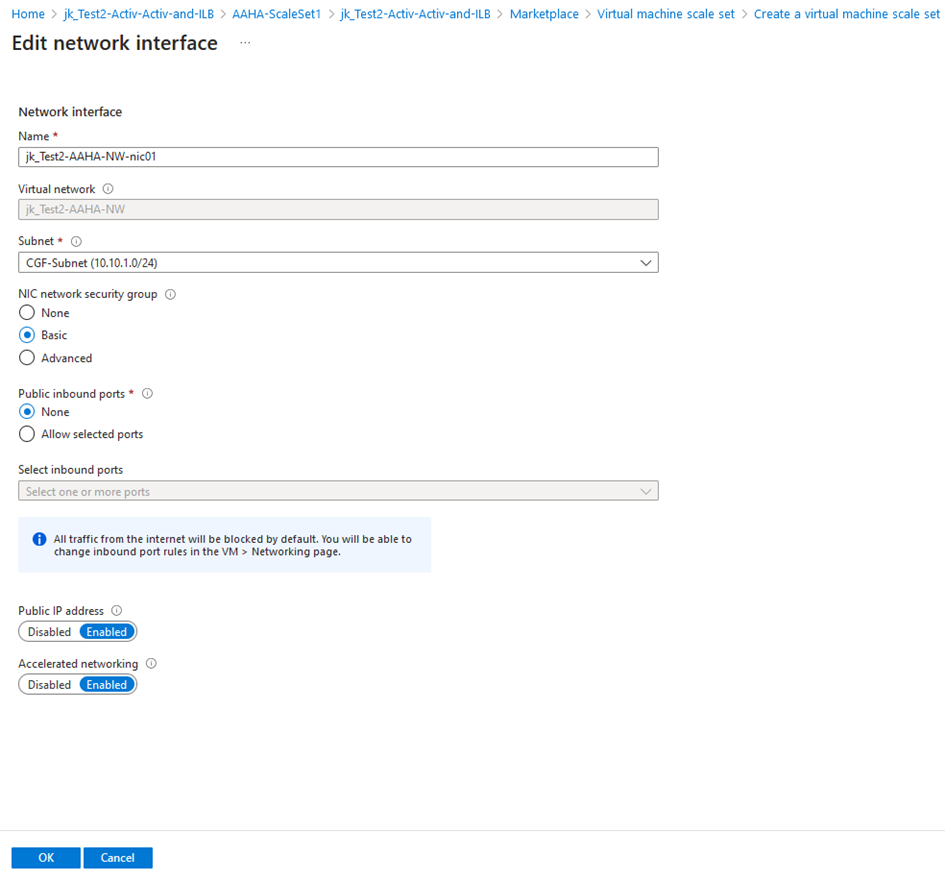
Repeat the previous sub steps for any additionally required network interface.
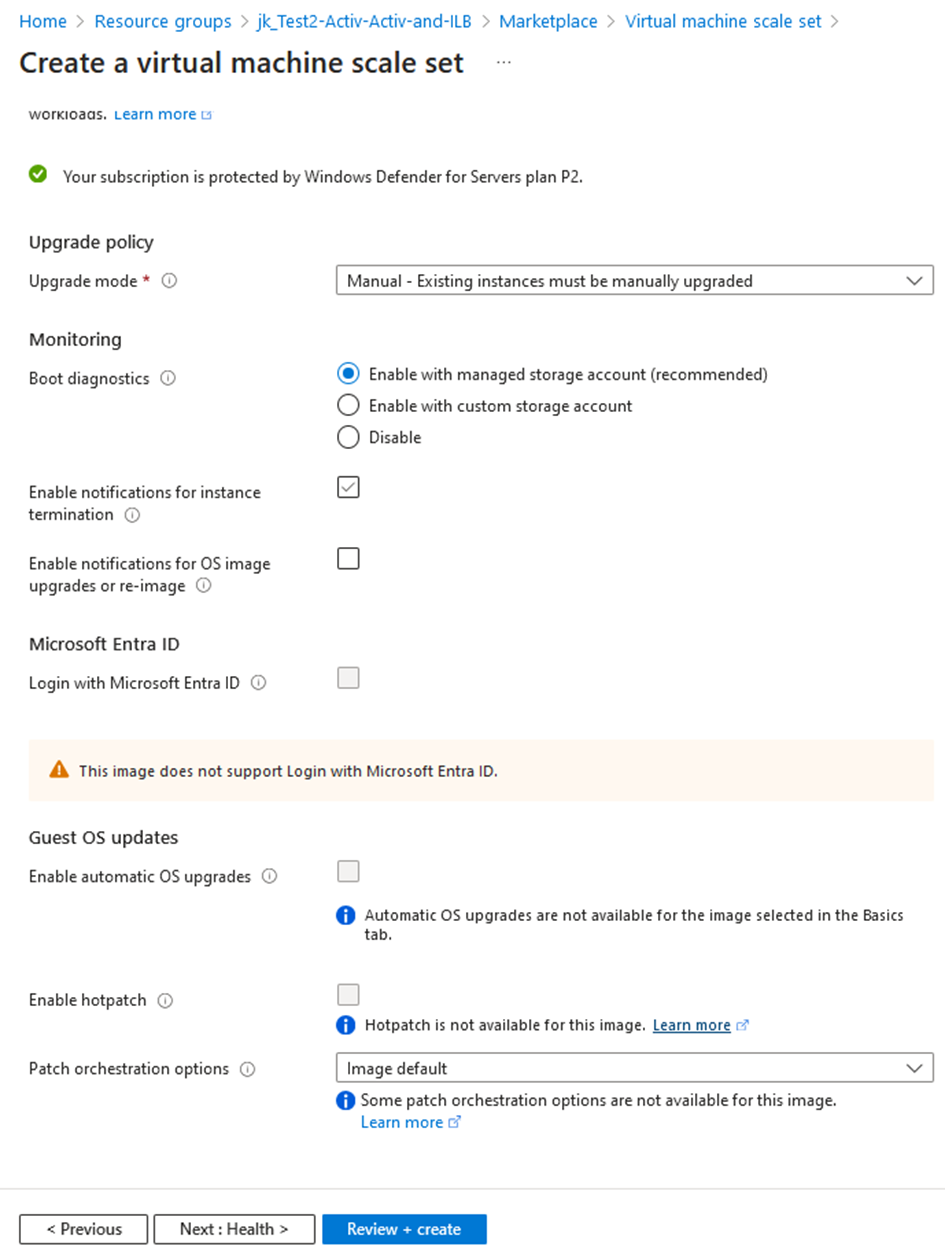
Step 6. Click the Management tab to Configure Settings for Managing the Setup
Configure the following options according to the screenshot below:
Step 7. Click and Configure Advanced settings
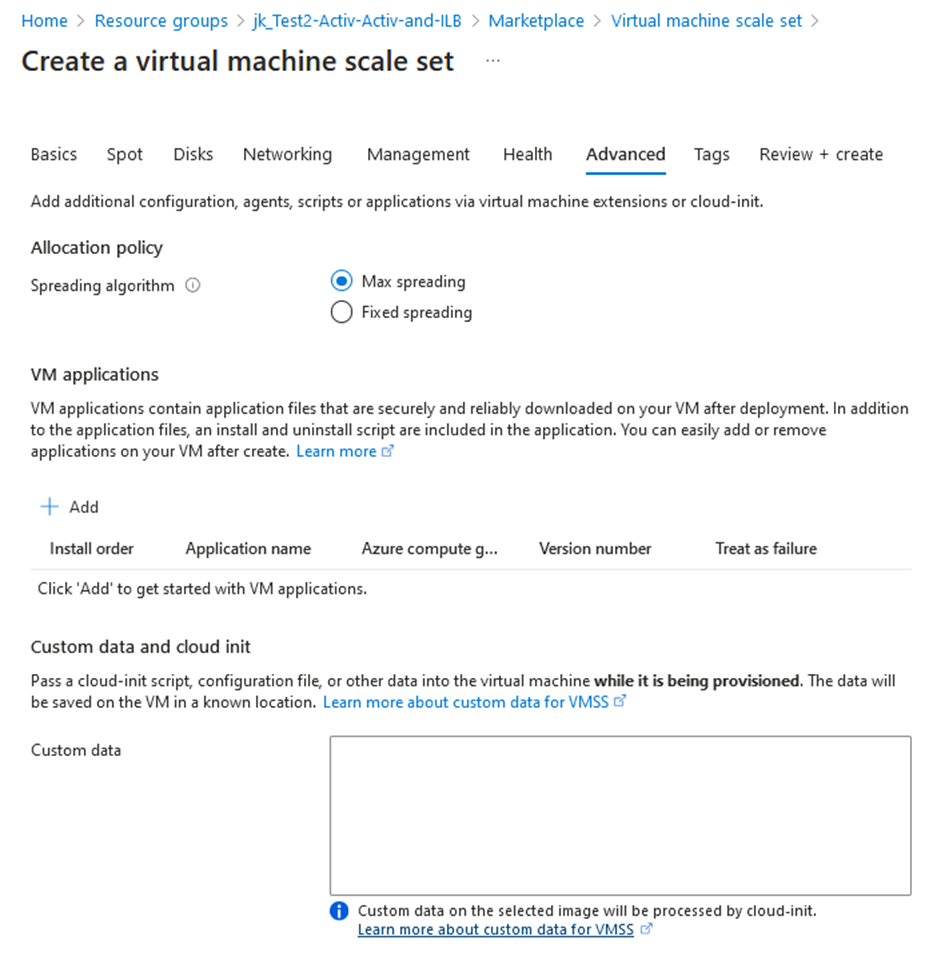
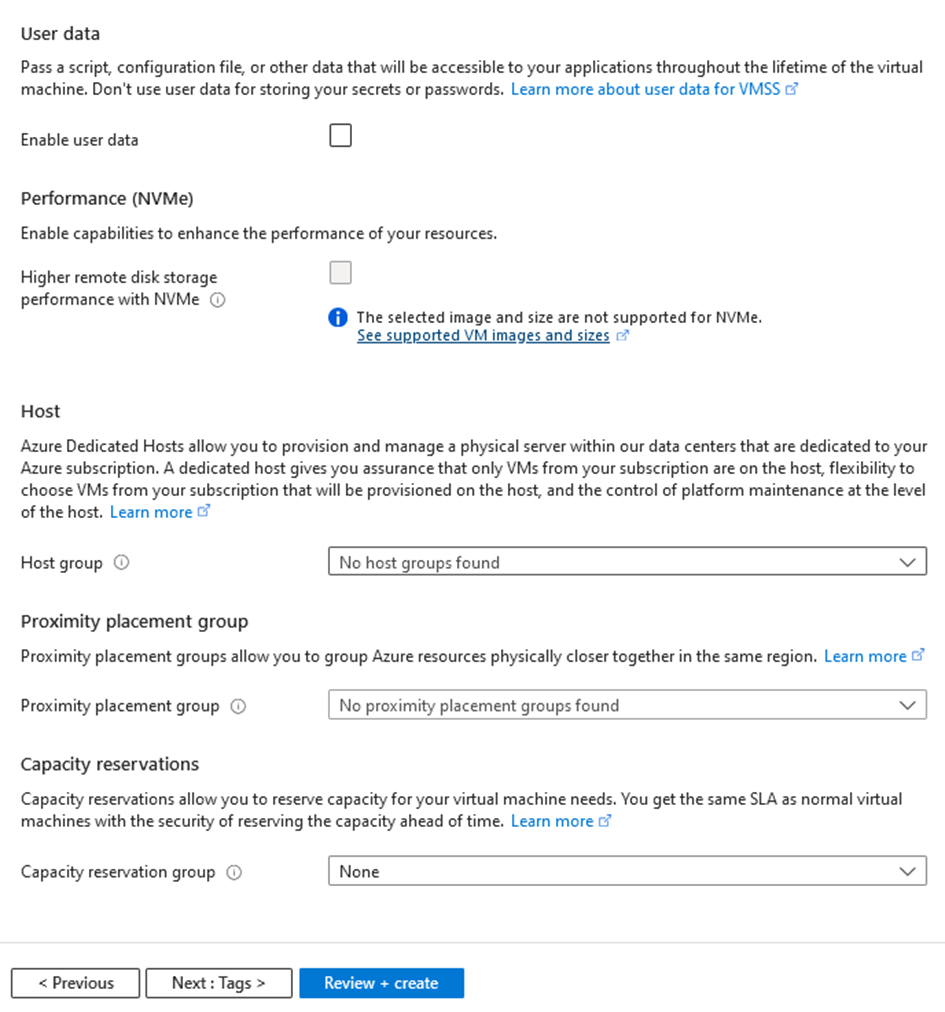
Step 8. Click Review + Create to Review the Configuration
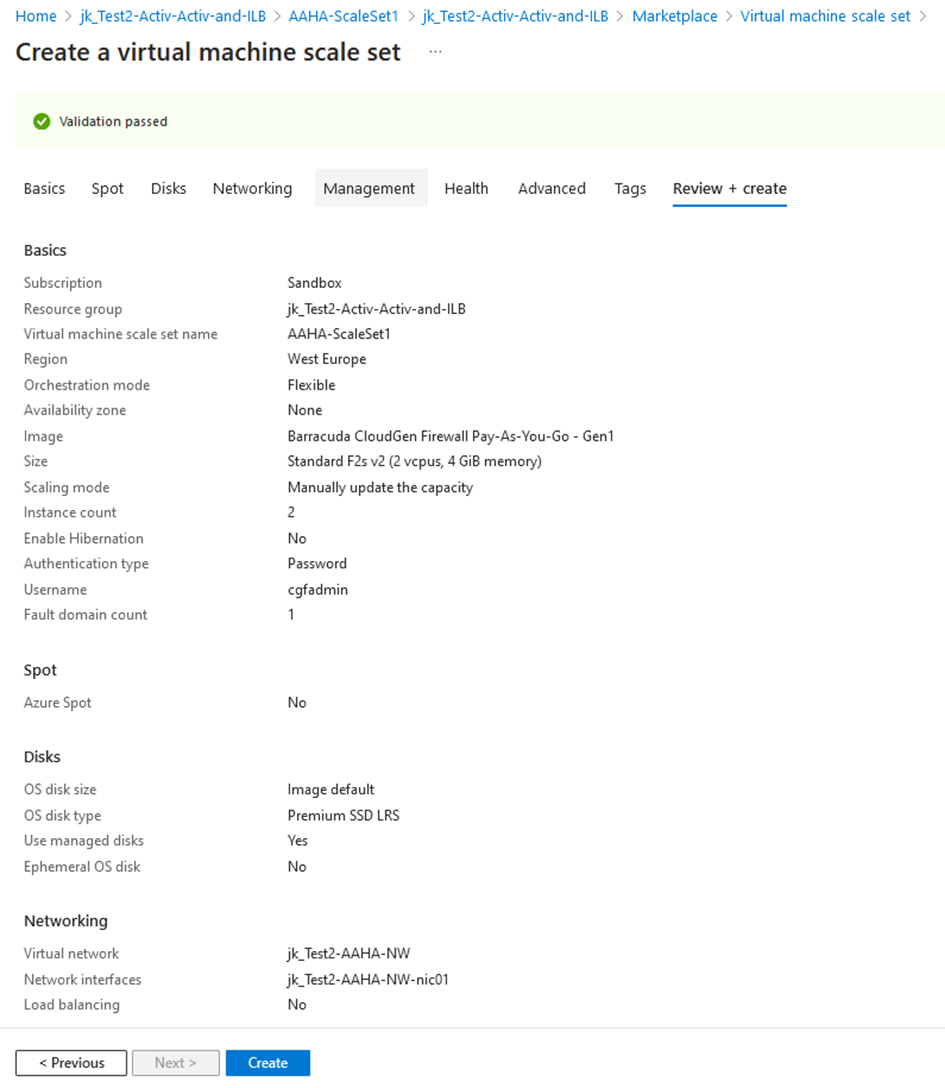
After completing the configuration of all required settings, click Create.
2. Virtual Machine Scale Set - Post Deployment Steps
Open the Virtual Machine Scale Set:
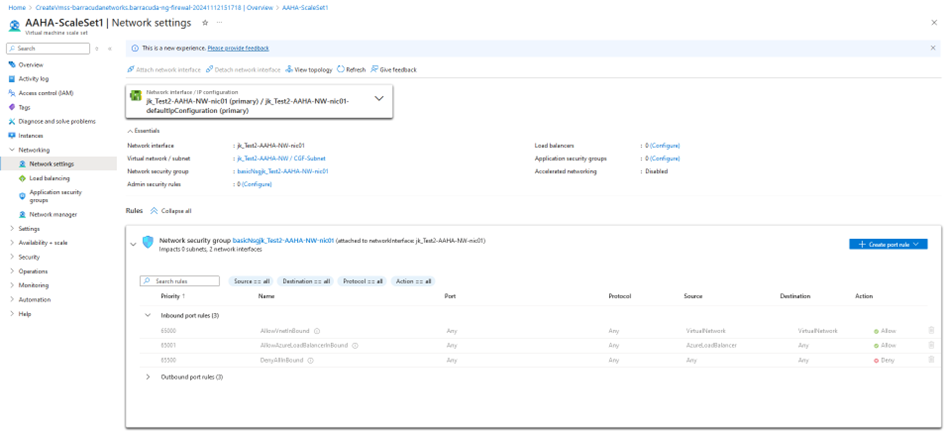
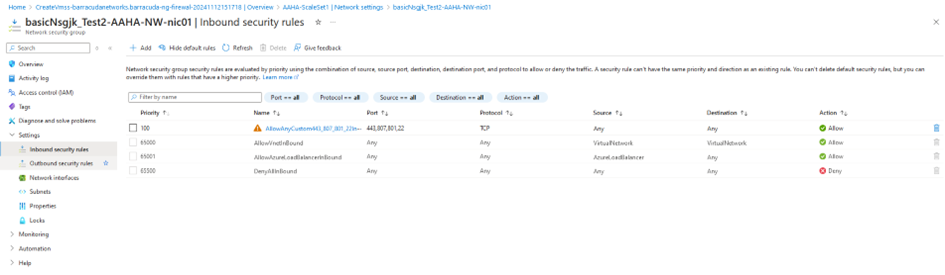
Select the Network Security Group and add Inbound Rules:
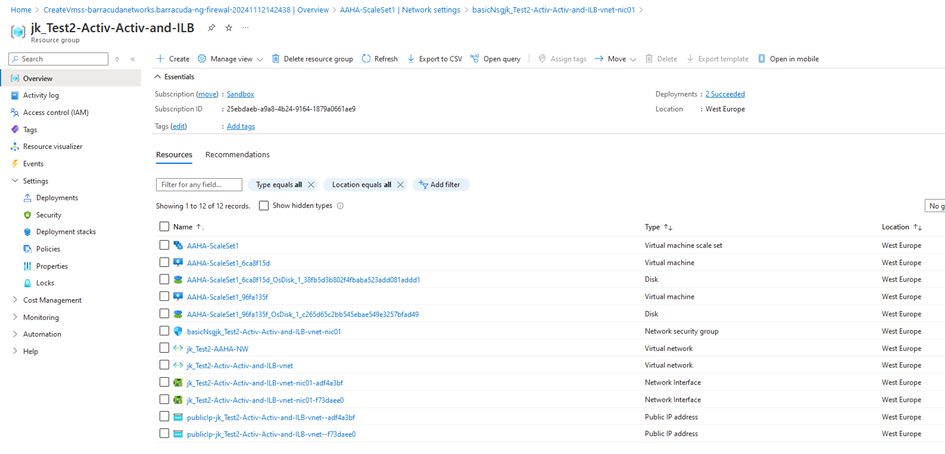
Go back to the Resource Group and check the Network Interface(s):
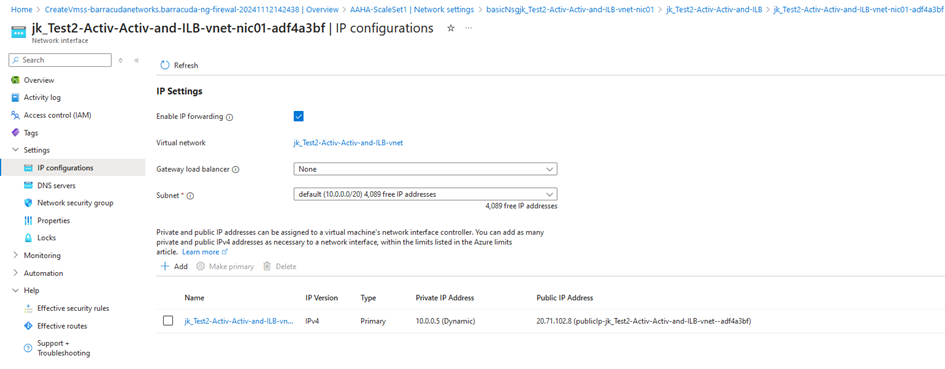
Enable IP Forwarding:
3. Create an Internal Load Balancer
Enter the required data to configure the internal load balancer:
Subscription – Select your subscription from the list.
Resource Group – Select your resource group from the list.
Name – Enter a name for your load balancer.
Region – Select the region from the list.
SKU – Select Standard.
Type – Select Internal
Tier – Regional
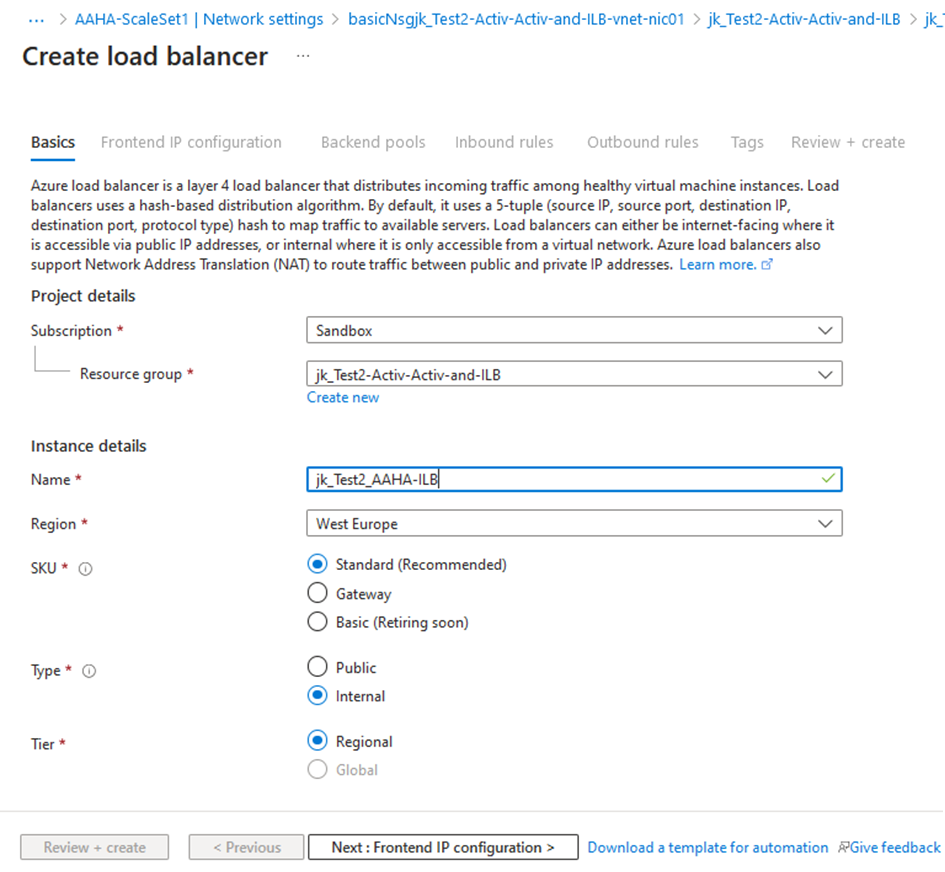
Click Next: Frontend IP configuration.
Enter the required data to configure the frontend IP address:
Subnet – Select the specific subnet from the list.
Assignment – Select Static.
IP address – e.g., 10.10.1.6
Availability zone – Select Zone-redundant from the list.
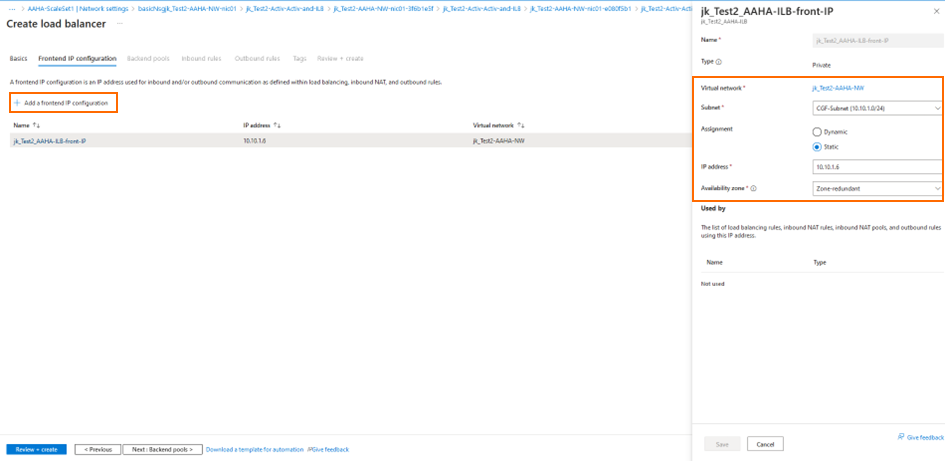
Click NEXT: Backend Pools
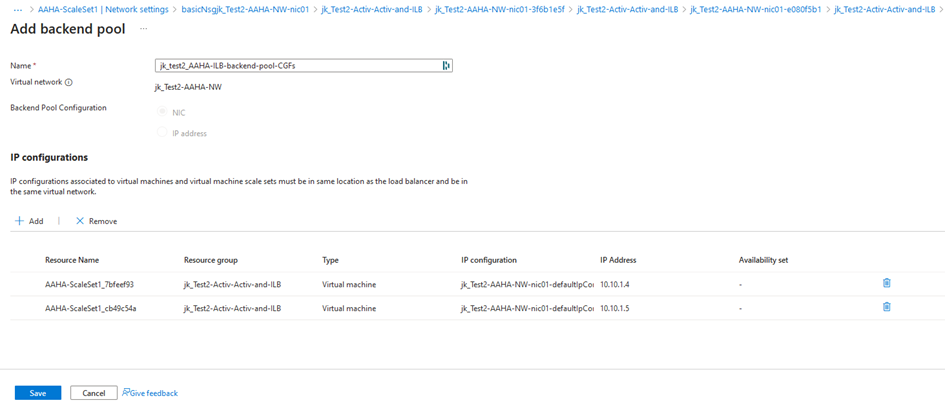
Click Save
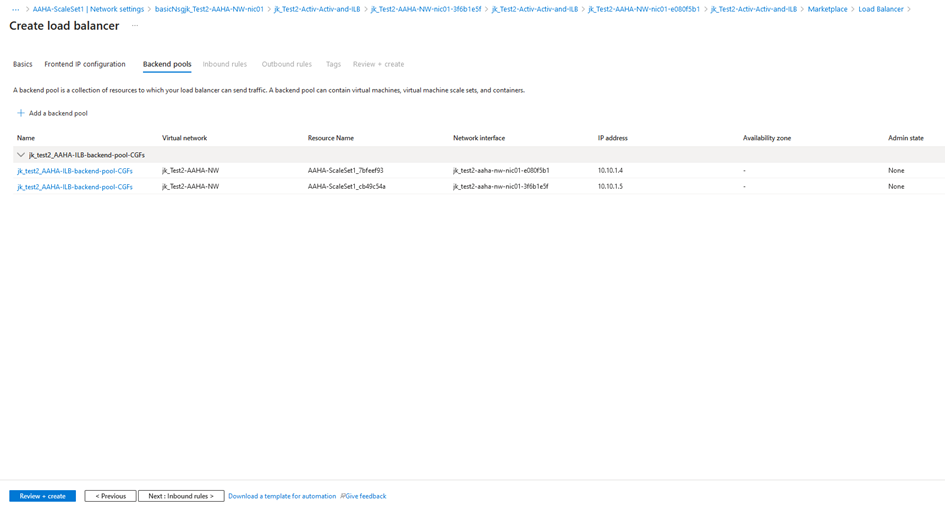
Click NEXT: Inbound rules
Enter the required data to configure the inbound rules:
IP Version – Select IPv4.
Frontend IP address – Select the required frontend IP address from the list.
Backend pool – Select the required backend pool from the list.
Select High availability ports.
Health probe – Select TCP 65000 from the list.
Idle timeout (miunutes) – select 4 from the list.
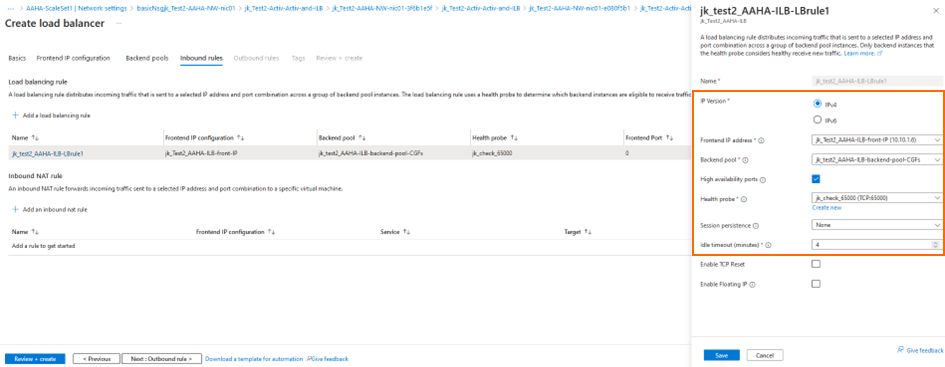
Click NEXT: Outbound rules
Click NEXT: Tags
Click NEXT: Review + create
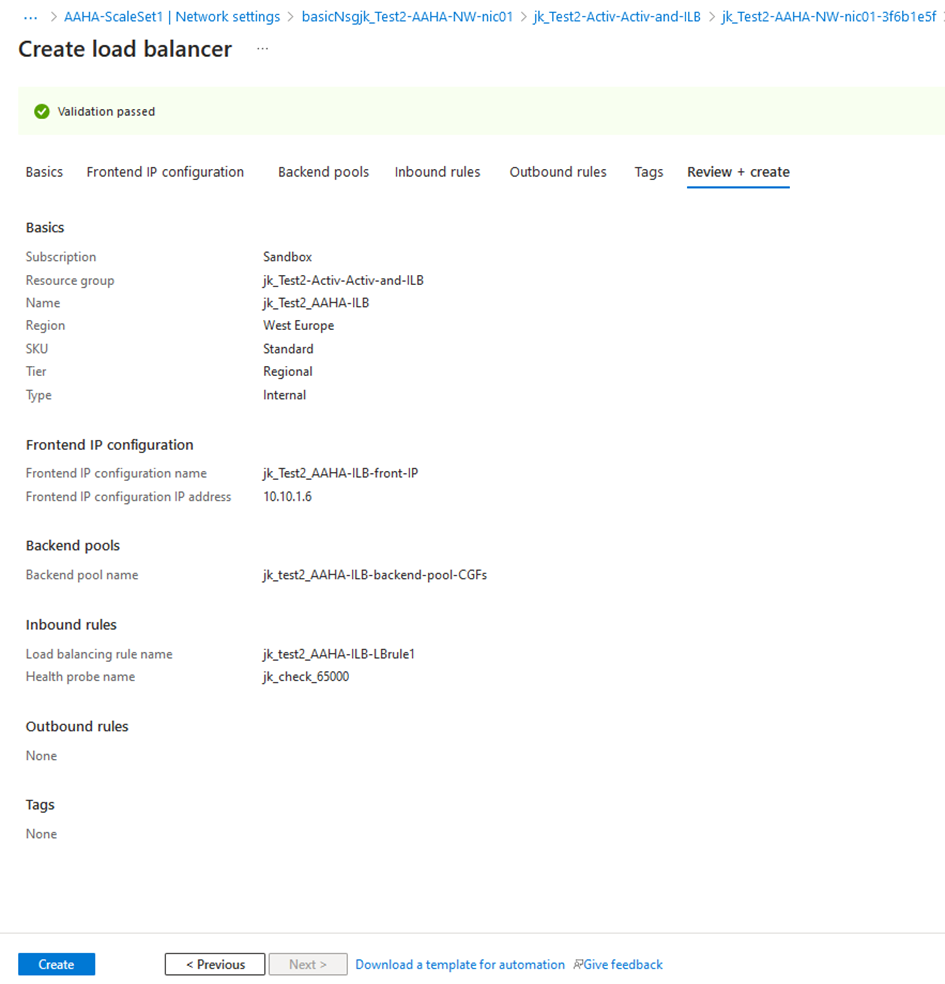
Check that all settings correspond with your requirements.
If you want to change a specific setting, navigate back to the related configuration template by clicking < Previous.
Click NEXT: Create
4. Create a User Defined Route Table
Locate and click the label Create Route Table.
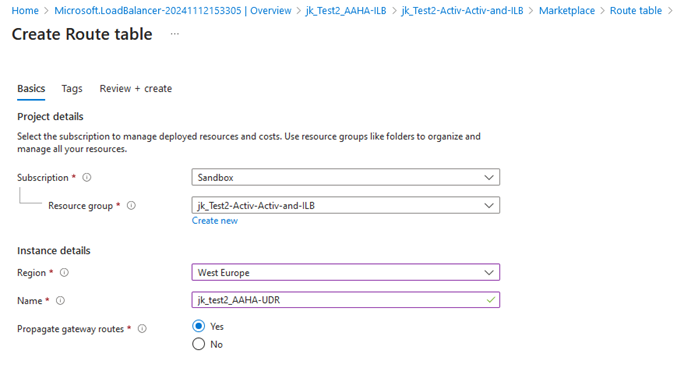
Click Review + create
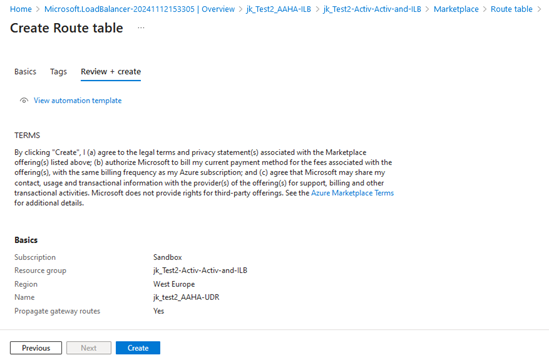
Click Create
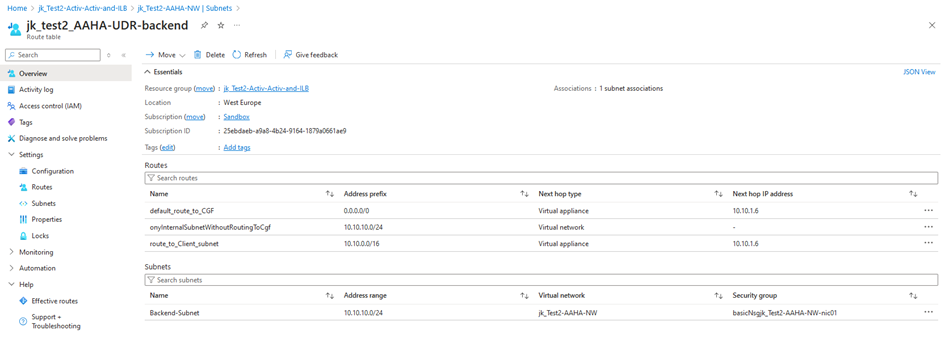
Add a default route and routes to all internal subnets:
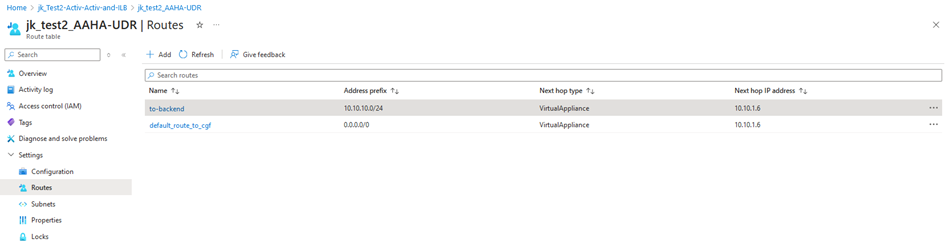
Add all internal subnets to be routed over the CGF:
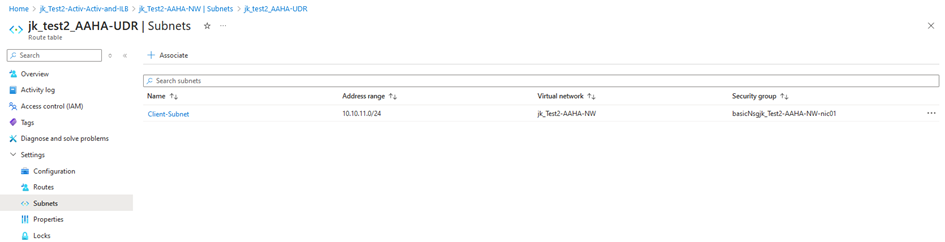
This screenshot shows an example related to the diagram at the top of this article:
Step 5. Add the Firewall Instances to the Control Center
Add the CloudGen Firewall instances created with the Firewall VM scale set to the Control Center. For more information on managed firewalls, please refer to How to Import an Existing CloudGen Firewall into a Control Center.
Create a cluster- / range-level repository for the linked configuration management. For more information, see Repositories.
Step 6. Set Up Rules and Repositories, and Link Them to Your Firewall Scale Set
On the Control Center, go to Configuration Tree > your Range > your Cluster > your Box > Assigned Services > Firewall.
Right-click Forwarding Rules and select Copy to Cluster repository.
Provide a Name and copy the node.
Open the created repository.
Click Lock.
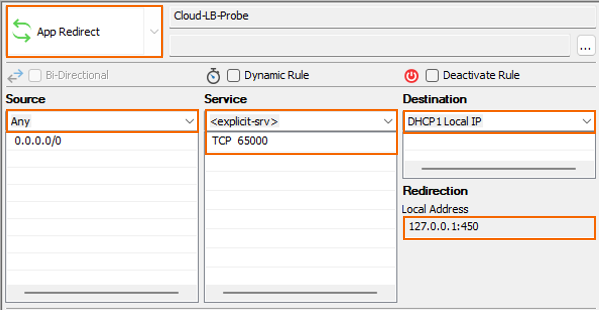
Add an App Redirect Rule rule for load balancing heath check.
Source – Select Any.
Services – Add
65000 TCPDestination – Select DHCP1 Local IP.
Redirection – Enter
127.0.0.1:450
Add a Dst NAT rule to access the back-end server:
Source – Select Any.
Services – Add the ports for required services.
Destination – Select DHCP1 Local IP.
Redirection – Enter the IP address of your back-end server.
Connection Method – select Original Source IP.
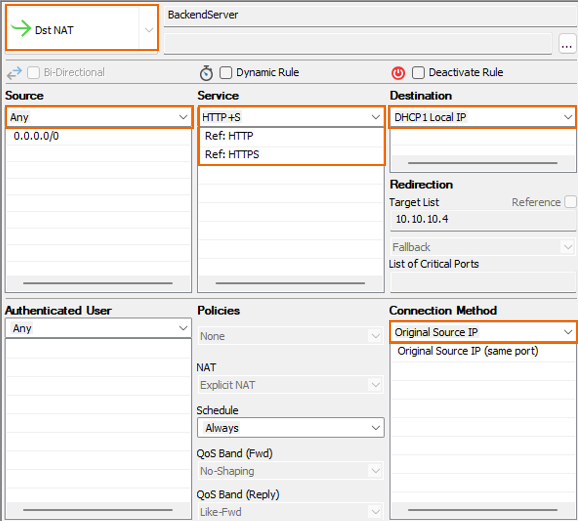
Click OK.
Click Send Changes.
Close the repository window.
Right-click on the firewall repository and select Multiple Object Action.
Select all firewall instances for the corresponding scale set.
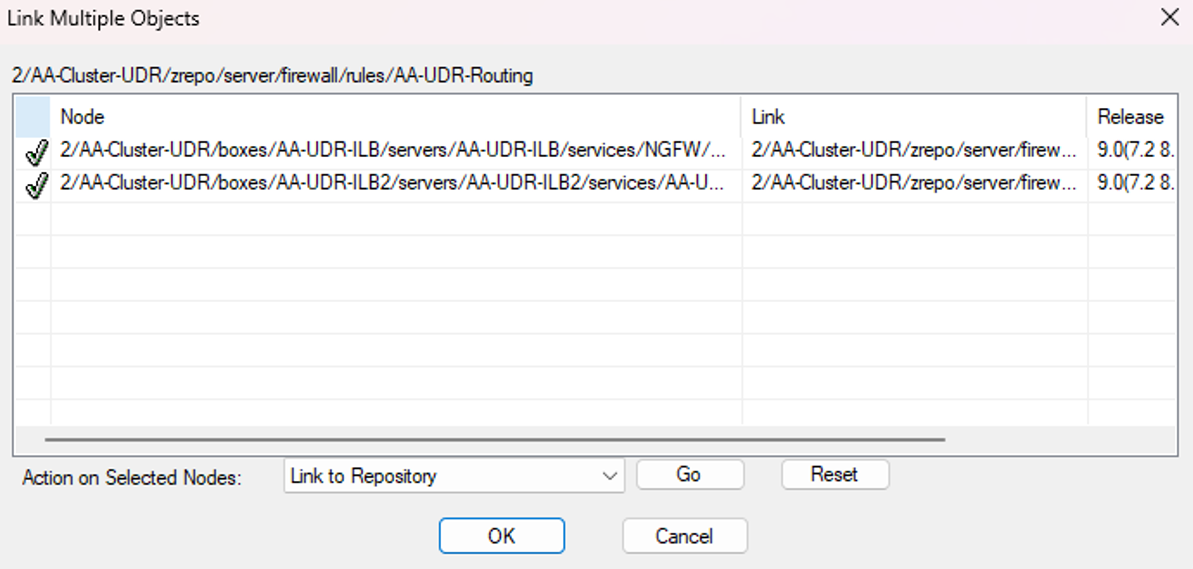
Select Link To repository > Go.
Click OK.
Click Activate.
Step 7. Verify the Setup
Your Barracuda CloudGen Firewall instances are now fully integrated in the Azure cloud and communicate with the load balancer that processes traffic from and to your subnets. To verify that your CloudGen Firewalls are up and running, go to Firewall > Live. The traffic details for your CloudGen Firewalls should be listed with the configured rules.
All instances from subnets associated with the route table should be able to reach the ILB Front IP.
All instances from subnets associated with the route table should be able to reach the back-end services.
Next Steps
You can now configure your routing rules on the CloudGen Firewalls according to individual requirements.
