The Barracuda Load Balancer ADC increases the scalability and reliability of your Moodle deployment.
Product Versions and Prerequisites
You must have:
- Barracuda Load Balancer ADC version 5.1 or 5.2.
- Moodle 2.6 or earlier versions.
- Installed your Barracuda Load Balancer ADC(s), connected to the web interface, and activated your subscription(s).
Terminology
Before you begin deploying the Barracuda Load Balancer ADC with Moodle, familiarize yourself with these terms:
Term | Definition |
|---|---|
Moodle | Modular Object-Oriented Dynamic Learning Environment. A free software e-learning platform or a course management system that provides easy-to-edit, secure, and structured course web sites. |
NFS | Network File System. Lets machines mount a disk partition on a remote machine as if it were a local disk. It allows for fast, seamless sharing of files across a network. |
Fully Qualified Domain Name (FQDN) | The unique name for a specific computer or host that can resolve to an IP address (e.g., www.example.com). |
Service | A combination of a virtual IP (VIP) address and one or more TCP/UDP ports that the Barracuda Load Balancer ADC listens on. Traffic arriving over the specified port(s) is directed to one of the real servers associated with a particular service. |
Instant SSL | Instant SSL provides SSL (HTTPS) access to content on servers without having to modify the servers or the content on the servers. The Barracuda Load Balancer ADC rewrites the "http" links in the response to "https". |
Moodle Services Deployment Options
Deployments of Moodle services are supported in either a one-armed or a two-armed topology. This can be either a single or multiple subnet configuration. Unless the users must directly access individual servers, it is recommended that you place the servers in one or more subnets that are reachable by an internal-facing port of the Barracuda Load Balancer ADC. If users must directly access individual servers, a one-armed deployment is recommended.
Direct Server Return (DSR) is not supported in a Moodle services deployment.
You can create either an Instant SSL or HTTP service. If you want to enforce encryption for all connections to your Moodle servers, create an Instant SSL service. Otherwise, create an HTTP service.
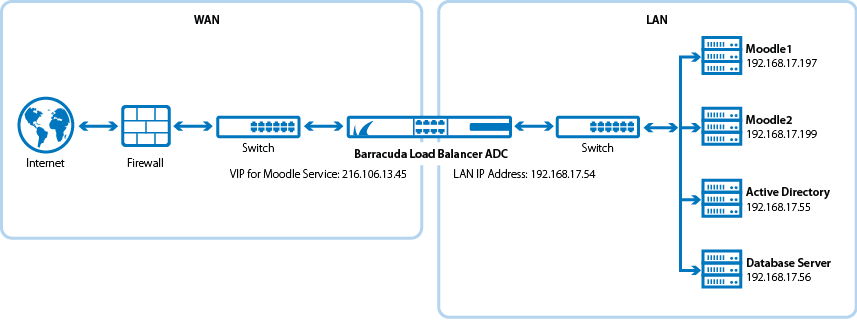
The following diagram shows an example of how the Barracuda Load Balancer ADC can be deployed with Moodle services in a web farm.
Deployment Scenario
Deploy the Barracuda Load Balancer ADC for Moodle
To deploy the Barracuda Load Balancer ADC for Moodle services in a web farm, complete the following steps :
Step 1. Install Moodle in a Web Farm
Install the latest Moodle software on the back-end servers.
It is recommended that you place the database on a separate server. You can use either NFS or Samba to share the Moodle database between the database server and the back-end servers.
Step 2. Create Services on the Barracuda Load Balancer ADC
You can create either an Instant SSL or HTTP service. If you want to enforce encryption for all connections to your Moodle servers, create an Instant SSL service. Otherwise, create an HTTP service.
Create an Instant SSL Service
- Log into the Barracuda Load Balancer ADC as the administrator.
- Go to the BASIC > Certificates page and create the required certificate.
- Go to the BASIC > Services page.
Click Add Service and enter the values in the corresponding fields.
Name
Type
IP Address
Port
HTTP Service Port SSL Settings Certificates Load Balancing Moodle_InstantSSL
Instant SSL
The IP address of the FQDN that clients use to access.
For example, 10.5.7.205.
443
80 - Secure Site Domain – Enter the domain name of your Moodle server. If the internal and external domain are different, you can use wildcard characters. For example: *.barracuda.com
If your Barracuda Load Balancer ADC is running version 5.1.1 and above, set the Rewrite Support option to On. For versions below 5.1.1, this option is named Instant SSL.
Select the certificate that you uploaded for the service. - Persistence Type – Select Source IP.
- Persistence Netmask – Enter: 255.255.255.255
- Click Add Server to configure the real servers. In the server settings, ensure that you:
- Enter the IP addresses of the back-end servers. For example, 192.168.17.197 and 192.168.17.199.
- Use port 80.
- If traffic must be encrypted when it is passed to the real servers, enable Server uses SSL. Otherwise, non-encrypted traffic is passed to the real servers because the Barracuda Load Balancer ADC decrypts the incoming traffic.
If the Moodle server uses compression, configure the web translations. By default, the Barracuda Load Balancer ADC does not decompress encoded content. If the Moodle servers use compression, create an HTTP Request Rewrite condition to remove the Accept-Encoding header.
- Go to the TRAFFIC > Web Translations page.
In the HTTP Request Rewrite section, create the following rule:
Rule Name Sequence Number
Action
Header Name
Old Value
Rewrite Condition
Remove_Encoding 2 Remove Header Accept-Encoding * *
Create an HTTP Service
- Log into the Barracuda Load Balancer ADC as the administrator.
Go to the BASIC > Services page.
Click Add Service and enter the values in the corresponding fields.
Name
Type
IP Address
Port
Load Balancing Moodle_HTTP
HTTP
The IP address of the FQDN that clients use to access.
80
- Persistence Type – Select Source IP.
- Persistence Netmask – Enter: 255.255.255.255
- Click Add Server to configure the real servers. In the server settings, ensure that you:
- Enter the IP addresses of the back-end servers. For example, 192.168.17.197 and 192.168.17.199.
- Use port 80.
