Follow the steps in this guide to deploy the Barracuda Load Balancer ADC to increase the scalability and reliability of your Microsoft Active Directory Federation Services (AD FS) deployment. The Barracuda Load Balancer ADC also improves the performance of AD FS by balancing the authentication requests that are sent to your AD FS servers.
Terminology
| Term | Definition |
|---|---|
| Fully Qualified Domain Name (FQDN) | The unique name for a specific computer or host that can resolve to an IP address (for example, www.example.com). |
| VIP | Virtual IP address. In the Barracuda Load Balancer ADC deployment, the VIP is added to the service on the Barracuda Load Balancer ADC. |
| Service | A combination of a virtual IP address and one or more TCP/UDP ports that the Barracuda Load Balancer ADC listens on. Traffic arriving on the specified port(s) is directed to one of the real servers associated with a service. |
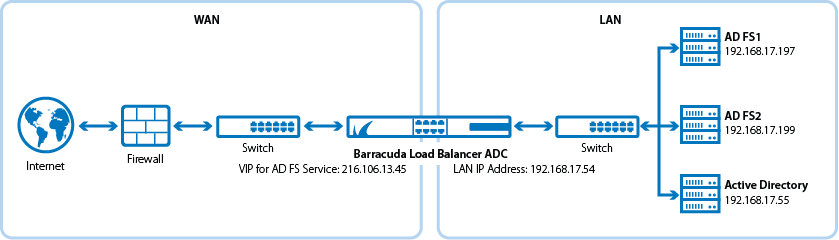
Deployment Scenario
Product Versions and Prerequisites
You must have:
- Barracuda Load Balancer ADC version 5.1 or 5.2.
- Active Directory Federation Services ( AD FS) 2.0 or above (Windows Server 2012 R2). It is strongly recommended that you use Windows Server 2012 R2 and AD FS 3.0.
- A fully configured AD FS farm with at least two servers.
- Installed your Barracuda Load Balancer ADC(s), connected to the web interface, and activated your subscription(s).
- If you want to deploy AD FS with high availability, cluster your Barracuda Load Balancer ADCs. For more information, see High Availability.
Step 1. Set Up and Deploy the AD FS Farm
Configure at least two separate servers with the AD FS service that you want to load balance. Test the login page on each AD FS server to ensure that AD FS is working. The URL is usually something like:
https://<fqdn of adfs>/adfs/ls/IdpInitiatedSignon.aspx
For example: https://adfs-1/adfs/ls/IdpInitiatedSignon.aspx
Complete the test by logging in with an Active Directory account.
Figure 1. Default AD FS Login Page
Step 2. Create Services on the Barracuda Load Balancer ADC
- Log into the Barracuda Load Balancer ADC as the administrator.
- Go to the BASIC > Certificates page, and create or import the required certificate. If you import a certificate, ensure that it is the same certificate that you configured AD FS with.
Go to the BASIC > Services page, and create the service listed in the following table. To add a real server, click Add Server.
Name Type IP Address Port Session Timeout Persistence Real Servers ADFS_HTTPS HTTPS The VIP address for the AD FS service. For example: 10.5.7.193 443 600 - Type : Source IP
- Time: 1200 seconds
- IP addresses of the AD FS servers
- Port: 443
- Enable SSL on both servers
- Upload or select the certificate you configured the AD FS service with
Enable Server Name Identification (SNI) by scrolling to SSL Settings and opening the Advanced Options. Enable SNI and then add each SNI domain by clicking Add SNI Domain. Enter the domain name and the associated certificate (the same certificate you configured AD FS with). Complete this step for each SNI domain. Client requests for domains that are not associated with any certificate will get the default certificate.
Step 3. Configure the DNS
Create an A record to point the VIP address that you set on the Barracuda Load Balancer ADC for the AD FS service.
For example, if you want to use the name sso and your domain is barracuda.com, your A record would look something like this:
| Name | IP Address |
|---|---|
| sso.barracuda.com | 10.5.7.193 |
Step 4. Test your Load Balanced AD FS Setup
Go to the AD FS login page using the name that you set in the A record and verify that the page displays correctly. The URL is usually something like:
https://<fqdn of adfs>/adfs/ls/IdpInitiatedSignon.aspx
For e xample, if you set sso as the new name, go to:
https://sso.barracuda.com/adfs/ls/IdpInitiatedSignon.aspx
