Required Product Version
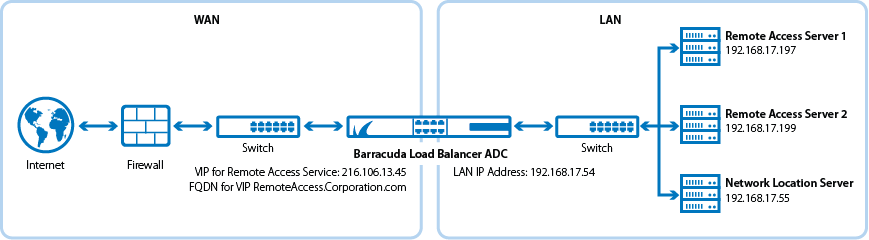
This article describes how to deploy your Barracuda Load Balancer ADC version 5.1 or 5.2 with Microsoft® Remote Access.The Barracuda Load Balancer ADC increases the performance and reliability of Microsoft Remote Access Service (Direct Access and VPN) by load balancing between multiple Remote Access servers.
To Deploy your Barracuda Load Balancer ADC with Microsoft's Remote Access Services, complete the following steps:
Terminology
Term | Definition |
|---|---|
| Domain Controller | A server that responds to security authentication requests. |
| Service | Defined by a combination of a virtual IP (VIP) address and one or more TCP/UDP ports that the Barracuda Load Balancer ADC listens on. Traffic arriving over the specified ports is directed to one of the real servers associated with that service. |
| TCP Proxy | Makes the Barracuda Load Balancer ADC act as a full proxy. Connections from the client are terminated at the Barracuda Load Balancer ADC, and new connections are established between the Barracuda Load Balancer ADC and the real servers. |
| Fully Qualified Domain Name (FQDN) | The unique name for a specific computer or host that can resolve to an IP address (for example, www.example.com). |
| Network Location Server | The network location server is a key component of DirectAccess. It detects whether computers configured as DirectAccess clients are located in the corporate network. When clients are in the corporate network, DirectAccess is not used to reach internal resources. Instead, clients connect to internal resources directly. |
Deployment Scenario
Microsoft TechNet References
See the following Microsoft TechNet article, Plan a Remote Access Cluster Deployment, for instructions on how to set up a load balanced cluster:
Prerequisites
To complete this procedure, you must have the following:
- Windows Server 2012 or newer. Barracuda Networks recommends using the latest release of Windows Server.
- The Barracuda Load Balancer ADC must be connected to the web interface with its subscription activated.
- If you want to deploy Remote Access Services with high availability, cluster two or more Barracuda Load Balancer ADCs. For more information, see High Availability.
Step 1. Configure the Servers
- Set up the Windows Servers that provide the Microsoft Remote Access Services with the Direct Access and VPN (Or just Direct Access or VPN service) in a Load Balanced Cluster setup environment (see the TechNet article referenced above for instructions).
- Barracuda Networks recommends the Behind an edge device (with single network adapter) deployment scenario.
- Set up the Network Location Server on a separate server that is not your Remote Access (Direct Access and VPN) Server (Microsoft supports installing Network Location Server properties on the same server as your Remote Access server but is not recommended in a load balanced environment).
- Ensure that the FQDN of the Network Location Server is reachable from the internal (corporate) network from the clients you wish to deploy this on.
- Ensure that on all deployed client computers, Remote Access is added to the Security Group configured on Remote Access.
Step 2. Create Services on the Barracuda Load Balancer ADC
Add the following TCP Proxy service on the Load Balancer ADC:
| Name | Type | IP Address | Port | Load Balancing | Server Monitor |
|---|---|---|---|---|---|
| RemoteAccessProxy | TCP Proxy | VIP Address for the FQDN of the host used by Clients to Connect to the Remote Access Server For example: 216.46.173.5 | 443 | Set Persistence Type to Source IP with the appropriate netmask | Set Testing Method to TCP Port Check |
Step 3. Add the Real Servers
Add your Remote Access servers to your service. For each Remote Access Server:
On the BASIC > Services page, verify that the correct service for the server is displayed
- Click Add Server.
- Enter the IP address of the server with port 443.
- If the server is part of a cluster, specify if it is a Backup server and enter its Weight for the load balancing algorithm.
- Click Create.
Step 4. Verify Your Configuration
- Log in to one of the clients configured for Remote Access while it is off the internal (corporate) network and ensure that the Workplace Connection is in the connected state.
- If you opted for just VPN, test the VPN connection configured on a client while it is off the internal (corporate) network and ensure that the client is able to connect.
