Step 1 - Download the Certificate
Use the following steps to download the certificate from the Barracuda Web Application Firewall:
- Log into the Barracuda Web Application Firewall web interface, and go to the BASIC > Certificates page.
- In the Saved Certificates table, locate the certificate, and click Certificate in the Download column.
- In the Save Token page, enter a pass phrase in the Encryption Password field, and click Save.
- The certificate is exported as a PKCS #12 token, which includes the private key.
Step 2 - Extract the Private Key
This section describes how to extract the private key from a PKCS #12 file using OpenSSL.
If the private key is encrypted, use the following steps to extract the private key from the PKCS #12 token and decrypt the private key on either a Linux system or a Windows system.
- If you are using a Windows system, open a command prompt and change the working directory to the one where you installed OpenSSL so that you can run OpenSSL from the command line:
C:\OpenSSL-Win32\bin\> - Enter the following command to simultaneously extract and encrypt the private key. This command looks for the certificate file in the C:\\OpenSSL-Win32\bin\folder. If the file is located in a different drive or folder, prefix the path to the file name accordingly.
openssl pkcs12 -nocerts -in certificate.pfx -out private_key_encrypted.pem - When prompted, enter the password you assigned when downloading the .pfx file from the Barracuda Web Application Firewall in point 3 in the section Step 1 - Downloading the Certificate.
- (Optional) You can export the signed certificate using the following command:
openssl pkcs12-nokeys –nodes -in certificate.pfx -out signed_cert.cer - (Optional) You can decrypt the encrypted private key using the following command:
openssl rsa -in private_key_encrypted.pem -out private_key_decrypted.pem
Step 3 - Get the Intermediate and Root Certificates
You can download the intermediate and root certificates of most certificate authorities (CAs) using Microsoft® Internet Explorer ® . However, you may need to follow the support link on the CA site to obtain the correct intermediate and root certificates.
- On the system where you downloaded the certificate, double-click the downloaded certificate, for example, mycertificate.cer, and click the Certificate Path tab.
- Double-click each CA in the issuer hierarchy, and note the details, including the name of the issuer and the certificate expiry date. These details are helpful in identifying the intermediate and root certificates in the steps that follow.
- Open Internet Explorer, and go to Tools > Internet Options > Content > Certificates .
- Click the Intermediate Certification Authorities tab, and select the relevant certificate.
- Click Export. Follow the instructions in the Wizard, exporting the certificate as Base-64 encoded X.509 (.CER), and saving the export with the appropriate name.
- In the Certificates page, click the Trusted Root Certification Authorities tab, and select the root certificate.
- Click Export. Follow the instructions in the Wizard, exporting the certificate as a Base-64 encoded X.509 (.CER), and saving the export with an appropriate name.
- Because Internet Explorer adds trailing line breaks to files, open each exported file in a basic editing program such as WordPad or Notepad++ (do not use Notepad), and remove any trailing line breaks.
Step 4 - Upload the Certificate
Use the following steps to upload the certificate chain in the correct order, using the screenshot for reference:
- In the Barracuda Web Application Firewall web interface, go to the BASIC > Certificates page.
- In the Upload Certificate section, enter a name for the certificate in the Certificate Name field.
- Select the Certificate Type as PEM Certificate.
- Select the key/algorithm used in the certificate.
- RSA - RSA is a public-key cryptography algorithm.
- ECDSA - Elliptic Curve Digital Security Algorithm (ECDSA) is a digital signature algorithm which uses Elliptic Curve Cryptography (ECC).
- In the Signed Certificate field, click Browse, and navigate to and select the Server Certificate.
- Set Assign Associated Key to No.
- In the Certificate Key field, click Browse, and navigate to and select the Private Key.
- In the intermediary Certificates field, click Browse, and navigate to and select the Intermediate Certificate.
- Click the plus ( + ) symbol following the Intermediary Certificates field.
- In the new intermediary Certificates field, click Browse, and add the second Intermediate Certificate.
- Click the plus ( + ) symbol following the Intermediary Certificates field, navigate to and select the Root Certificate.
- Select Yes for Allow Private Key Export.
- Click Upload Now to upload the certificate.
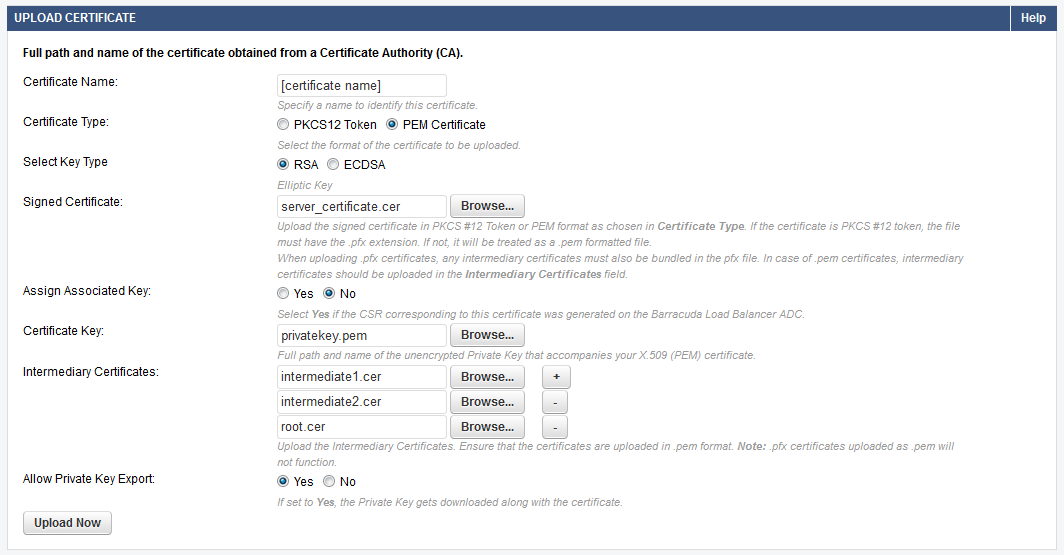
The uploaded certificate displays in the Upload Certificates section of the Saved Certificates table .
